-
Keywords: civil liberties, privacy, data protection, freedom of information, human rights
- Edward Snowden's Privacy Tips: "Get Rid Of Dropbox", Avoid Facebook And Google | TechCrunch, 11-okt-2014
- June 5th is Coming: Actions on the Anniversary of the First Snowden Release | Electronic Frontier Foundation, 22-mei-2014
- No Place To Hide: Edward Snowden, the NSA, and the U.S. Surveillance State by Glenn Greenwald | Documents (COMPRESSED) [pdf] | Documents (UNCOMPRESSED) [pdf] | Notes [pdf] | Index from No Place to Hide [pdf]
- Abhörskandal: James Clapper gesteht Überwachung von Amerikanern ein | Spiegel Online, 2-apr-2014
- Wyden, Udall on Revelations that Intelligence Agencies Have Exploited Foreign Intelligence Surveillance Act 'Loophole' Press Release | U.S. Senator Ron Wyden, 1-apr-2014
- James R. Clapper letter to US senator Ron Wyden 28-mrt-2014 | US senator Wyden's website [pdf]
there have been queries
- NSA surveillance program reaches - into the past - to retrieve, replay phone calls | The Washington Post, 18-mrt-2014
- How the NSA Plans to Infect 'Millions' of Computers with Malware by Ryan Gallagher and Glenn Greenwald | The Intercept, 12-mrt-2014
Top-secret documents reveal that the National Security Agency is dramatically expanding its ability to covertly hack into computers on a mass scale by using automated systems that reduce the level of human oversight in the process.
The classified files - provided previously by NSA whistleblower Edward Snowden - contain new details about groundbreaking surveillance technology the agency has developed to infect potentially millions of computers worldwide with malware "implants." The clandestine initiative enables the NSA to break into targeted computers and to siphon out data from foreign Internet and phone networks - President Obama's speech on NSA surveillance reforms - full text | theguardian.com, 17-jan-2014
- Obama's NSA 'reforms' are little more than a PR attempt to mollify the public | | Comment is free | The Guardian Glenn Greenwald | The Guardian, 17-jan-2014
Ultimately, the radical essence of the NSA - a system of suspicion-less spying aimed at hundreds of millions of people in the US and around the world - will fully endure even if all of Obama's proposals are adopted. That's because Obama never hid the real purpose of this process. It is, he and his officials repeatedly acknowledged, "to restore public confidence" in the NSA. In other words, the goal isn't to truly reform the agency; it is deceive people into believing it has been so that they no longer fear it or are angry about it.
As the ACLU's executive director Anthony Romero said after the speech:
The president should end - not mend - the government's collection and retention of all law-abiding Americans' data. When the government collects and stores every American's phone call data, it is engaging in a textbook example of an 'unreasonable search' that violates the constitution.
That, in general, has long been Obama's primary role in our political system and his premiere, defining value to the permanent power factions that run Washington. He prettifies the ugly; he drapes the banner of change over systematic status quo perpetuation; he makes Americans feel better about policies they find repellent without the need to change any of them in meaningful ways. He's not an agent of change but the soothing branding packaging for it.
As is always the case, those who want genuine changes should not look to politicians, and certainly not to Barack Obama, to wait for it to be gifted. Obama was forced to give this speech by rising public pressure, increasingly scared US tech giants, and surprisingly strong resistance from the international community to the out-of-control American surveillance state.- Neue Dokumente: Der geheime Werkzeugkasten der NSA Von Jacob Appelbaum, Judith Horchert, Ole Reißmann, Marcel Rosenbach, Jörg Schindler und Christian Stöcker | Spiegel Online, 30-dec-2013
Die NSA hat eine geheime Abteilung, die Spezialausrüstung herstellt: Spähsoftware für Rechner und Handys, Mobilfunk-Horchposten, manipulierte USB-Stecker und unsichtbare Wanzen. Hier sehen Sie Auszüge aus dem hausinternen Bestellkatalog der Abteilung ANT - Preise inklusive. In unserer Grafik können Sie knapp 50 Seiten aus dem ANT-Katalog durchblättern - sortiert nach dem potentiellen Einsatzort und um Namen und E-Mail-Adressen von Mitarbeitern bereinigt. Es gibt "Implantate", wie die NSA das nennt, für Rechner, Server, Router und Hardware-Firewalls, Spezialausrüstung zum heimlichen Mitlesen auf dem Monitor einer Zielperson und Wanzen, die zwar lauschen, aber nicht funken - ihre Signale werden mit Radarwellen ausgelesen. Viele sind dafür gemacht, die technische Infrastruktur von Telekommunikationskonzernen zu unterwandern, um sie unbemerkt für NSA-Zwecke zu missbrauchen, oder um Unternehmensnetze anzuzapfen
| Interaktive Grafik: Hier sitzen die Späh-Werkzeuge der NSA | Spiegel Online, dec-2013- Quantumtheory: Wie die NSA weltweit Rechner hackt von Jacob Appelbaum, Marcel Rosenbach, Jörg Schindler, Holger Stark und Christian Stöcker | Spiegel Online, 30-dec-2013
Zum Arsenal der NSA gehört eine Methode, mit der sich nahezu jeder Rechner unbemerkt mit Späh-Software bestücken lässt. Streng geheime Dokumente zeigen, wie das System genau funktioniert
| NSA-Dokumente: So knackt der Geheimdienst Internetkonten | NSA-Dokumente: So übernimmt der Geheimdienst fremde Rechner- EFF Statement on President's Review Group's NSA Report | EFF, 18-dec-2013
The President's Review Group today recognized the severe risks caused by the government's mass spying on Americans and people around the world, joining the global consensus that the NSA has gone too far. The group's report included over 40 recommendations for promoting transparency, protecting online security tools, and making organizational reforms to the NSA, the Foreign Intelligence Surveillance Court and the civil liberties oversight bodies
- NSA review panel findings: Liberty and Security in a Changing World | The Guardian, 18-dec-2013
The Review Group on Intelligence and Communications Technology has released its 300-page report outlining 46 recommendations for the NSA
- Meet CO-TRAVELER: The NSA's Cell Phone Location Tracking Program | EFF
An article yesterday in the Washington Post disclosed the NSA's massive cell phone location program. The program, codenamed CO-TRAVELER, is designed to track who meets with whom and covers everyone who carries a cell phone, all around the world
- Special supplement on the NSA files | The Guardian, 2-dec-2013
- NSA: Geheimdokument offenbart Vierjahresplan des Geheimdiensts von Matthias Kremp | Spiegel Online, 24-nov-2013
- A Strategy for Surveillance Powers NSA document | NYTimes.com, 23-feb-2012
Values
We will constantly strive to improve our knowledge, our people, our technology, and our products.
Through innovation and personalization, we will advance the SIGINT system. Our customers and stakeholders can rely on us to provide timely, high quality products and services, because we never stop innovating and improving, and we never give up!
The Environment
As the world has changed, and global interdependence and the advent of the information age have transformed the nature of our target space, we have adapted in innovative and creative ways that have led some to describe the current day as "the golden age of SIGINT".
The interpretation and guidelines for applying our authorities, and in some cases the authorities themselves, have not kept pace with the complexity of the technology and target environments, or the operational expectations levied on NSA's mission.
Digital information created since 2006 grew tenfold, reaching 1.8 exabytes in 2011, a trend projected to continue; ubiquitous computing is fundamentally changing how people interact as individuals become untethered from information sources and their communications tools; and the traces individuals leave when they interact with the global network will define the capacity to locate, characterize and understand entities.
Expectations
For SIGINT to be optimally effective, legal, policy, and process authorities must be as adaptive and dynamic as the technological and operational advances we seek to exploit. Nevertheless, the culture of compliance, which has allowed the American people to entrust NSA with extraordinary authorities, will not be compromised in the face of so many demands, even as we aggressively pursue legal authorities and a policy framework mapped more fully to the information age.
SIGINT Goals for 2012-2016
1.1. Through advanced tradecraft and automation, dramatically increase mastery of the global network
2. Fully leverage internal and external NSA partnerships to collaboratively discover targets, find their vulnerabilities, and overcome their network/communication defenses.
2.1.2. Counter the challenge of ubiquitous, strong, commercial network encryption
2.2. Defeat adversary cybersecurity practices in order to acquire the SIGINT data we need from anyone, anytime, anywhere- Snowden-Dokumente: NSA infizierte 50.000 Netzwerke mit überwachungs-Software | Zeit Online, 23-nov-2013
- Inside the "Electronic Omnivore": New Leaks Show NSA Spying on U.N., Climate Summit, Text Messaging | Democracy Now!, 4-nov-2013
As Edward Snowden seeks clemency from the United States, the New York Times has revealed new details about how the National Security Agency is spying on targets ranging from the United Nations to foreign governments to global text messages. We are joined by New York Times reporter Scott Shane, who reports that the NSA has "as an electronic omnivore of staggering capabilities, eavesdropping and hacking its way around the world to strip governments and other targets of their secrets, all the while enforcing the utmost secrecy about its own operations." The Times article reveals how the NSA intercepted the talking points of U.N. Secretary-General Ban Ki-moon ahead of a meeting with President Obama in April and mounted a major eavesdropping effort focused on the United Nations climate change conference in Bali in 2007. The Times also reveals the existence of an NSA database called Dishfire that "stores years of text messages from around the world, just in case." Another NSA program called Tracfin "accumulates gigabytes of credit card purchases."
- Privacy and surveillance: Jacob Applebaum, Caspar Bowden and more | World news | Liveblog | theguardian.com, 30-sep-2013
- Spilling the NSA's Secrets: Guardian Editor Alan Rusbridger on the Inside Story of Snowden Leaks | Democracy Now!, 23-sep-2013
Three-and-a-half months after National Security Agency leaker Edward Snowden came public on the the U.S. government’s massive spying operations at home and abroad, we spend the hour with Alan Rusbridger, editor-in-chief of The Guardian, the British newspaper that first reported on Snowden’s leaked documents. The Guardian has continued releasing a series of exposés based on Snowden’s leaks coloring in the details on how the NSA has managed to collect telephone records in bulk and information on nearly everything a user does on the Internet. The articles have ignited widespread debate about security agencies’ covert activities, digital data protection and the nature of investigative journalism. The newspaper has been directly targeted as a result - over the summer the British government forced the paper to destroy computer hard drives containing copies of Snowden’s secret files, and later detained David Miranda, the partner of Guardian journalist Glenn Greenwald. Rusbridger, editor of The Guardian for nearly two decades, joins us to tell the inside story of The Guardian’s publication of the NSA leaks and the crackdown it has faced from its own government as a result
- Linus Torvalds Talks Linux Development at LinuxCon 18-sep-2013
NSA Backdoor
Torvalds was also asked if he had ever been approached by the U.S. government to insert a backdoor into Linux.
Torvalds responded "no" while nodding his head "yes," as the audience broke into spontaneous laughter- 5 PRISM-blikken op oude incidenten door Jasper Bakker | Webwereld, 14-sep-2013
- NSA vermomde zich als Google | Automatisering Gids, 13-sep-2013
- Canada Facilitated NSA's Effort To Weaken Encryption Standards by Michael Geist, 11-sep-2013
- Government Releases NSA Surveillance Docs and Previously Secret FISA Court Opinions In Response to EFF Lawsuit | EFF, 10-sep-2013
The Director of National Intelligence (DNI) just today released hundreds of pages of documents related to the government's secret interpretation of Patriot Act Section 215 and the NSA's (mis)use of its massive database of every American's phone records. The documents were released as a result of EFF's ongoing Freedom of Information Act lawsuit
- Hundreds of Pages of NSA Spying Documents to be Released As Result of EFF Lawsuit| EFF, 5-sep-2013
In a major victory in one of EFF's Freedom of Information Act (FOIA) lawsuits, the Justice Department conceded yesterday that it will release hundreds of documents, including FISA court opinions, related to the government's secret interpretation of Section 215 of the Patriot Act, the law the NSA has relied upon for years to mass collect the phone records of millions of innocent Americans
- National Security Letter: Dokument belegt Google-überwachung | Spiegel Online, 28-aug-2013
- Google Motion in re NATIONAL SECURITY LETTER
- Open Secret About Google's Surveillance Case No Longer Secret | WSJ, 26-aug-2013
- Miranda Detention: 'Blatant Attack on Press Freedom by Laura Poitras, Spiegel Online, 27-aug-2013 | ReaderSupportedNews
The detention of David Miranda ... and the destruction of hard drives in the British newspaper's basement reveal one thing: Governments do not want their citizens to be informed when it comes to the topic of surveillance
- NSA Revelations of Privacy Breaches 'the Tip of the Iceberg' - Senate Duo by Spencer Ackerman, Guardian UK, 17-aug-2013 | ReaderSupportedNews
- NSA Spokesman Accidentally Admits that the Government Is Spying On All Americans by WashingtonsBlog | Dark Politricks, 21-jul-2013
- James Bamford on NSA Secrets, Keith Alexander's Influence & Massive Growth of Surveillance, Cyberwar | Democracy Now!, jun-2013 [video report]
As the U.S. vows to take "all necessary steps" to pursue whistleblower Edward Snowden, James Bamford joins us to discuss the National Security Agency's secret expansion of government surveillance and cyberwarfare. In his latest reporting for Wired magazine, Bamford profiles NSA Director Gen. Keith Alexander and connects the dots on PRISM, phone surveillance and the NSA's massive spy center in Bluffdale, Utah. Says Bamford of Alexander: "Never before has anyone in America's intelligence sphere come close to his degree of power, the number of people under his command, the expanse of his rule, the length of his reign or the depth of his secrecy." The author of "The Shadow Factory: The Ultra-Secret NSA from 9/11 to the Eavesdropping on America," Bamford has covered the National Security Agency for the last three decades, after helping expose its existence in the 1980s
- Meet PRISM's little brother: Socmint by Paul Wright, wired.co.uk | Ars Technica, 26-jun-2013
For the past two years, a tight-lipped and little talked about unit within the Metropolitan Police has been conducting blanket surveillance of British citizens' public social media conversations. Following an unintentional leak and a detailed investigation, we are finally able to see some of the capabilities of this 17-man team-some of which are truly alarming
- Netzschnöffelei der US-Regierung: Nicht mit unseren Servern | taz.de, 8-jun-2013
- VS verzamelen online privégegevens van gebruikers 7-jun-2013 | nrc.nl
- Through a PRISM darkly: Tracking the ongoing NSA surveillance story by Mathew Ingram | gigaom.com, 7-jun-2013
The past few days have seen a blizzard of leaks about surveillance activity by the government's ultra-secret NSA arm, including data collection from phone companies and internet giants. Here is what you need to know about this developing story
- Washington Post Began PRISM Story Three Weeks Ago, Heard Guardian's 'Footsteps' | Huffington Post, 7-jun-2013
The Washington Post revealed on Thursday the existence of a secret National Security Agency program code-named PRISM, which reportedly allows the U.S. government to tap directly into the servers of several major Internet companies, including Microsoft, Yahoo, AOL and Google.
The blockbuster story, which included PowerPoint slides provided by a "career intelligence official", landed online at 5:43 p.m. and led the front page Friday morning.
But roughly 20 minutes after the Post story appeared online Thursday, The Guardian -- which had already broken a major story the previous night on the NSA’s seizure of millions of Verizon customers’ phone records -- published its own story on PRISM, complete with PowerPoint slides. The Guardian's Glenn Greenwald, who broke the Verizon story, shared a byline on the PRISM story with Washington bureau chief Ewen MacAskill.
That two news outlets would publish stories on a secret government program so close together is striking, and the timing suggests there was a race to get the news up first. Indeed, Barton Gellman, who co-wrote the Post’s story, told The Huffington Post that he "started to hear some footsteps, so I had to move"- NSA Whistleblowers: All U.S. Citizens" Targeted by Surveillance Program, Not Just Verizon Customers | Democracy Now!, 6-jun-2013
- NSA Can Access Much of Americans' Digital Lives | ACLU, 6-jun-2013
- Massive NSA Phone Data-Mining Operation Revealed | ACLU, 5-jun-2013
Using the Patriot Act, the U.S. government has been secretly tracking the calls of every Verizon Business Network Services customer - whom they talked to, from where, and for how long - for the past 41 days, according to a report published by The Guardian
- Judge Orders Google to Turn over Data to FBI | newsmax.com, 31-mei-2013
U.S. District Court Judge Susan Illston on Tuesday rejected Google's argument that the so-called National Security Letters the company received from the FBI were unconstitutional and unnecessary. Illston ordered Google to comply with the secret demands even though she found the letters unconstitutional in March in a separate case filed by the Electronic Frontier Foundation.
She acknowledged as much in her four-page order in the Google case made on May 20 and obtained by The Associated Press on Friday- President Foreshadows New Internet Surveillance Proposal During National Security Speech 30-mei-2013 | EFF
But the first half of Obama’s statement-about "review[] the authorities of law enforcement, so we can intercept new types of communication"-is quite troubling. The line is likely an allusion to CALEA II, a dangerous proposal the New York Times has reported the administration "is on the verge of backing." The measure would force companies like Google and Facebook to install backdoors in all of their products to facilitate law-enforcement access, putting both our privacy and security at risk
- Congressman Preps Bill to End Terror War Authority by Spencer Ackerman, Wired | readersupportednews.org, 25-mei-2013
In the wake of President Obama's big speech about restraining the war on terrorism, a member of the House intelligence committee is working on a bill to undo the basic authorities to wage it
- Twitter Wikileaks Court Order | ACLU
- Privacy Loses in Twitter/Wikileaks Records Battle EFF, 10-nov-2011
- Judge Rules Against Privacy and Free Speech in Twitter/WikiLeaks Case | American Civil Liberties Union | ACLU, 10-nov-2011
A federal judge in Virginia ruled today that the government can collect the private records of three Twitter users as part of its investigation related to WikiLeaks. The court also refused to unseal or publicly list all orders and other court documents relating to the parties in the case, including orders that may have been sent to other companies besides Twitter.
[...] "Internet users don’t automatically give up their rights to privacy and free speech when they use services like Twitter," said Aden Fine, staff attorney for the ACLU Speech, Privacy and Technology Project. "The government shouldn’t be able to get this kind of private information without a warrant, and they certainly shouldn’t be able to do so in secret. An open court system is a fundamental part of our democracy, and the very existence of court documents should not be hidden from the public."Organisaties
NEDERLAND EN EUROPA
Zie Snowden Leaks in Nederland en EuropaAMERIKA
- American Civil Liberties Union (ACLU)
- Central Intelligence Agency (CIA) Independent agency
- Crocodyl: Collaborative research on corporations
- Cryptome.org Information source
- Defense Advanced Research Projects Agency (DARPA) part of Dept. Def (DoD)
- Democracy Now!
- Department of Homeland Security (DHS)
- Electronic Frontier Foundation (EFF)
- Federal Bureau of Investigation (FBI) part of Dept. Just (DOJ)
- Information Sharing Environment (ISE) part of the Office of the Director of National Intelligence (ODNI) | ISE Annual report 2012 30-jun-2012 [pdf] | Background and Authorities
In his immediate response to the Recommendations of the 9/11 Commission, the President issued Executive Order 13356, Strengthening the Sharing of Terrorism Information to Protect Americans, August 27, 2004. In it the President directed agencies to give the "highest priority" to the prevention of terrorism and the "interchange of terrorism information [both] among agencies" and "between agencies and appropriate authorities of States and local governments." The President further directed that this improved information sharing be accomplished in ways that "protect the freedom, information privacy, and other legal rights of Americans."
Section 1016 of the Intelligence Reform and Terrorism Prevention Act of 2004 , embraced the key principles of EO 13356 and directed the establishment of the Information Sharing Environment- National Security Agency / Central Security Service (NSA/CSS) part of Dept. Def (DOD)
- Office of the Director of National Intelligence (ODNI)
The U.S. Intelligence Community is a coalition of 17 agencies and organizations, including the ODNI, within the Executive Branch that work both independently and collaboratively to gather and analyze the intelligence necessary to conduct foreign relations and national security activities. Hover over each component for a brief description or for more detail visit: Members of the IC.
- Air Force Intelligence
- Department of the Treasury
- Army Intelligence
- Drug Enforcement Administration (DEA)
- Central Intelligence Agency (CIA)
- Federal Bureau of Investigation (FBI)
- Coast Guard Intelligence
- Marine Corps Intelligence
- Defense Intelligence Agency
- National Geospatial-Intelligence Agency
- Department of Energy (DoE)
- National Reconnaissance Office
- Department of Homeland Security (DHS)
- National Security Agency (NSA)
- Department of State
- Navy Intelligence
LEVERANCIERS
- Neue Dokumente: Der geheime Werkzeugkasten der NSA Von Jacob Appelbaum, Judith Horchert, Ole Reißmann, Marcel Rosenbach, Jörg Schindler und Christian Stöcker | Spiegel Online, 30-dec-2013
- Buggedplanet.info is about Signals Intelligence (SIGINT), Communication Intelligence (COMINT), Tactical and Strategical Measures used to intercept Communications and the Vendors and Governmental and Private Operators of this Technology; with section on Vendors of SIGINT/COMINT/LI and supporting Technologies and Systems | Netherlands | Metadata
- Booz Allen Hamilton
- Capgemini
- CSC
- Palantir
- Raytheon Company: Customer Success Is Our Mission | Raytheon Company: Command, Control, Communications, Computers and Intelligence (C4I)
Directing artillery. Routing aircraft. Flying satellites. When it comes to making order from disorder, nobody helps you complete the mission better than Raytheon
Juridisch
NEDERLAND EN EUROPA
Zie Snowden Leaks in Nederland en EuropaAMERIKA
- Privacy Oversight Board Agrees with EFF: Mass Surveillance Is Illegal and Must End | Electronic Frontier Foundation, 23-jan-2014
The Privacy and Civil Liberties Oversight Board (PCLOB) today issued a report strongly condemning the NSA's mass telephone records surveillance program. PCLOB is an independent and bipartisan panel appointed by the president to advise the government on ensuring privacy and civil liberties. The report determined that the program, which the administration claims is authorized under Section 215 of the Patriot Act, is illegal under the terms of that same law and doesn't actually keep us safe
- Oversight Board Calls for End of NSA Telephone Records Program | EPIC, 23-jan-2014
- Report on the Telephone Records Program, Conducted under Section 215 of the USA PATRIOT Act and on the Operations of the Foreign Intelligence Surveillance Court by the Privacy and Civil Liberties Oversight Board | EFF, 23-jan-2014 [pdf]
- In Historic Ruling, Federal Judge Declares NSA Mass Phone Surveillance is Likely Unconstitutional | EFF, 16-dec-2013 | Klayman et al. V. Obama et al. Memorandum Opinion by the US District Court for the District of Columbia, filed 16-dec-2013 [pdf]
The FISC orders governing the Bulk Telephony Metadata Program specifically provide that the metadata records may be accessed only for counterterrorism purposes (and technical database maintenance). Specifically, NSA intelligence analysts, without seeking the approval of a judicial officer, may access the records to obtain foreign intelligence information only through "queries" of the records performed using "identifiers," such as telephone numbers, associated with terrorist activity. An "identifier" (i.e., selection term, or search term) used to start a query of the database is called a "seed," and "seeds" must be approved by one of twenty-two designated officials in the NSA's Homeland Security Analysis Center or other parts of the NSA's Signals Intelligence Directorate. Such approval may be given only upon a determination by one of those designated officials that there exist facts giving rise to a "reasonable, articulable suspicion" ("RAS") that the selection term to be queried is associated with one or more of the specified foreign terrorist organizations approved for targeting by the FISC.
[...]
When an NSA intelligence analyst runs a query using a "seed," the minimization procedures provide that query results are limited to records of communications within three "hops" from the seed. [...] In plain English, this means that if a search starts with telephone number (123) 456-7890 as the "seed," the first hop will include all the phone numbers that (123) 456-7890 has called or received calls from in the last five years (say, 100 numbers), the second hop will include all the phone numbers that each of those 100 numbers has called or received calls from in the last five years (say, 100 numbers for each one of the 100 "first hop" numbers, or 10,000 total), and the third hop will include all the phone numbers that each of those 10,000 numbers has called or received calls from in the last five years (say, 100 numbers for each one of the 10,000 "second hop" numbers, or 1,000,000 total).
[...]
Third, the almost-Orwellian technology that enables the Government to store and analyze the phone metadata of every telephone user in the United States is unlike anything that could have been conceived in 1979. In Smith, the Supreme Court was actually considering whether local police could collect one person's phone records for calls made after the pen register was installed and for the limited purpose of a small-scale investigation of harassing phone calls. The notion that the Government could collect similar data on hundreds of millions of people and retain that data for a five-year period, updating it with new data every day in perpetuity, was at best, in 1979, the stuff of science fiction. By comparison, the Government has at its disposal today the most advanced twenty-first century tools, allowing it to "store such records and efficiently mine them for information years into the future." And these technologies are "cheap in comparison to conventional surveillance techniques and, by design, proceed [ ] surreptitiously," thereby "evad[ing] the ordinary checks that constrain abusive law enforcement practices: limited police . . . resources and community hostility" - Liberty and in a changing world: Report and Recommendations of The President's Review Group on Intelligence and Communications Technologies | White House.gov, 12-dec-2013 [pdf]
Background: Trade, Internet Freedom, and Other Goals
The US is committed to international economic competitiveness, to improvements in the international trade system, and to achievement of economic growth. The rules for international trade are crucial for the pervasively international conduct of commerce on the Internet, as well as for other sectors involved in international trade. Free trade agreements can contribute to economic growth. Unfortunately, foreign concerns about US surveillance threaten achievement of these various goals.
For example, the Transatlantic Trade and Investment Partnership (T- TIP) is a large and visible trade negotiation potentially affected by the recent surveillance leaks. The T-TIP talks were launched in 2013 as "an ambitious, comprehensive, and high-standard trade and investment agreement" designed to eliminate all tariffs on trade, improve market access on trade in services, and address a wide range of other impediments to trade. But strong concerns have been expressed about surveillance by European officials, as reflected in this statement by the EU Parliament Committee on Foreign Affairs: "With the damage to trust in the transatlantic relationship caused by NSA massive surveillance and lack of data privacy remedies for Europeans, the transatlantic economic relationship is at risk."
European officials have similarly expressed doubt about whether to continue the existing Safe Harbor agreement for transfer of personal information to the US, under which companies are able to comply with the stricter EU privacy laws. Although the precise impact on such future negotiations is unclear, such statements show the linkage between intelligence collection decisions and international trade negotiations.
The effects of concern with US surveillance on US trade in cloud computing and other online activities have drawn particular attention. The public cloud computing market for enterprises is growing rapidly. By 2016, it is estimated to reach $207 billion annually, more than double the 2012 level. As a result, cloud computing vendors not only have to retain existing customers but also must recruit new customers to maintain market share. In the wake of press reports on US surveillance, two studies estimated large losses in sales for US cloud computing providers, due to concerns overseas about the security of US providers and possible legal measures to limit use of US-based cloud providers by other countries. US-based information technology companies and trade associations have expressed strong concerns, fearing that Chinese, European, and other competitors will use the disclosures to promote their products over American exports - Bills Pending As of 9/11/13 that Relate to NSA Surveillance | CDT, 12-sep-2013
- FISA Court Releases Opinion Justifying NSA Call Records Program | American Civil Liberties Union, 17-sep-2013
- Legislation Related to the Attack of September 11, 2001 | Thomas
- NSA Documents Released to the Public Since June 2013 | American Civil Liberties Union
- The silent power of the N.S.A. | NYTimes.com, 27-mrt-1983
David Burnham is a reporter in The Times's Washington bureau. This article is adapted from Mr. Burnham's book ''The Rise of the Computer State,'' to be published by Random House in May. A Federal Court of Appeals recently ruled that the largest and most secretive intelligence agency of the United States, the National Security Agency, may lawfully intercept the overseas communications of Americans even if it has no reason to believe they are engaged in illegal activities. The ruling, which also allows summaries of these conversations to be sent to the Federal Bureau of Investigation, significantly broadens the already generous authority of the N.S.A. to keep track of American citizens. The decision by the United States Court of Appeals for the Sixth Circuit involves the Government surveillance of Abdeen Jabara, a Michigan-born lawyer who for many years has represented Arab-American citizens and alien residents, and reverses a 1979 ruling that the N.S.A.'s acquisition of Jabara's overseas messages violated his Fourth Amendment right to be free of ''unreasonable searches and seizures.'' Even while refusing the plaintiff's request for reconsideration, the Court curiously acknowledged the far-reaching nature of the case, recognizing that the N.S.A.'s interception of overseas telecommunications and their dissemination to ''other Federal agencies has great potential for abuse.'' The Court, however, held that the problem was ''a policy matter that lies in the domain of the executive or legislative branch of our Government.''
INTERNATIONAAL
- Necessary and Proportionate: International Principles on the Application of Human Rights to Communications Surveillance Final version 10-jul-2013
Overzicht
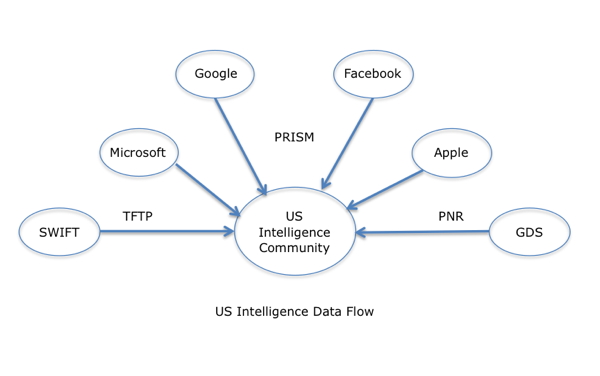
In juni 2013 werd op initiatief van Edward Snowden door The Guardian en de Washington Post informatie naar buiten gebracht over de levering van Internet-gegevens door Google, Facebook, Microsoft en Apple aan de Amerikaanse NSA (National Security Agency). Zie het volgende schema:
Later volgden onthullingen over het aftappen van transatlantische kabels door het Engelse GCHQ (Government Communications Headquarters) en het opzettelijk in gevaar brengen van de veiligheid van Internet en van de wereldbevolking door die Amerikaanse NSA, zie hierna.BELANGRIJKSTE LEAKS CHRONOLOGISCH
2013
2014
2015
Datum Bron Titel Betreft 19-feb The Intercept The Great SIM Heist: How Spies Stole the Keys to the Encryption Castle SIM codes
DIVERSE OVERZICHTEN
- The NSA Archive | American Civil Liberties Union
The ACLU and others have long suspected that the National Security Agency has gone far beyond its mandate of gathering information for counterterrorism and foreign intelligence purposes, implementing a massive spying system to conduct bulk surveillance of hundreds of millions of innocent Americans. Those suspicions were confirmed when, on June 5, 2013, The Guardian released the first in a series of documents provided by Edward Snowden detailing the NSA's unlawful spying activities. All of the documents released since that day -- both by the media and the government -- are housed in this database. Together, they have triggered a remarkable and long-overdue public debate about the legality and propriety of the government's surveillance practices.
You can search the text of the documents using the Keyword box to the right, and you can filter the documents using the tags below that box - NSA Spying | EFF.org | Timeline of NSA Domestic Spying
- US security state: In depth news, commentary and analysis from the Financial Times
- NSA: Chronologie der Enthüllungen von Edward Snowden | Golem.de
- Glossar zur NSA-Affäre: Marina, Prism, Noforn, Scissors, Pinwale, Sigad US-984XN | Golem.de
- The NSA files | GCHQ | The Guardian
- Prism Break Season 1 - (Episoden-Guide) | G! gutjahrs blog
Die Snowden-Saga folgt der Dramaturgie einer Fernsehserie. Woche für Woche neue Enthüllungen, neue Eskalationsstufen. Für alle, die den überblick verloren haben, hier der ultimative Episoden-Guide der ersten Staffel
- Timeline - NSA-Skandal: Was bisher geschah | Heise online
- NSA-Überwachungsskandal: Von NSA, GCHQ, BND, PRISM, Tempora, XKeyScore und dem Supergrundrecht - was bisher geschah | Heise online
- Tijdlijn NSA-schandaal | NOS Nieuws, 23-nov-2013
- New NSA Revelations Are Breaking Every Day | The Big Picture, 24-sep-2013
Spy Agencies Are Doing WHAT? Revelations about the breathtaking scope of government spying are coming so fast that it's time for an updated roundup
- SocioSite: Internet als SurveillanceStaat: Grootschalig afluisteren door de digitale snuffelstaat door dr. Albert Benschop, Universiteit van Amsterdam, gepubliceerd 4-okt-2013, updated 10-apr-2014
- Im Internet veröffentlichte Dokumente um den NSA-Skandal | Spiegel Online, 20-sep-2013
- Prism, Tempora, XKeyscore - NSA-überwachung im überblick | Spiegel Online, 22-jul-2013
- Meer over afluisterpraktijken NSA | Volkskrant.nl
Systemen en projecten
BOUNDLESS INFORMANT - NSA
Boundless Informant is het programma waarmee de aanwezigheid van metadata per land in kaart kan worden gebracht.
- Boundless Informant: the NSA's secret tool to track global surveillance data | The Guardian, 9-jun-2013
The National Security Agency has developed a powerful tool for recording and analysing where its intelligence comes from, raising questions about its repeated assurances to Congress that it cannot keep track of all the surveillance it performs on American communications.
| Boundless Informant NSA data-mining tool four key slides | The Guardian, 8-jun-2013
The Guardian has acquired top-secret documents about the NSA datamining tool, called Boundless Informant, that details and even maps by country the voluminous amount of information it collects from computer and telephone networks.
The focus of the internal NSA tool is on counting and categorizing the records of communications, known as metadata, rather than the content of an email or instant message.
The Boundless Informant documents show the agency collecting almost 3 billion pieces of intelligence from US computer networks over a 30-day period ending in March 2013. One document says it is designed to give NSA officials answers to questions like, "What type of coverage do we have on country X" in "near real-time by asking the SIGINT [signals intelligence] infrastructure" - NSA bouwt tool om inzicht te krijgen in aftapprogramma IT Pro - Nieuws | Tweakers, 9-jun-2013
De NSA zou een dataminingtool gebruiken om meer inzicht te krijgen in verkregen metadata. De tool, Boundless Informant geheten, zou inzicht geven tot de hoeveelheid verzamelde data per land
- Boundless Informant: NSA explainer | The Guardian, 8-jun-2013
View the three-page explanation document, which showed the NSA collected almost 3 billion pieces of intelligence from US computer networks over a 30-day period ending in March
- Boundless Informant: NSA explainer View the three-page explanation document, which showed the NSA collected almost 3 billion pieces of intelligence from US computer networks over a 30-day period ending in March document | documentcloud [pdf]
DISHFIRE - NSA
Dishfire is een database van SMS-berichten, waaruit het programma PREFER o.a. metadata zoekt uit standaard berichten over gemiste oproepen, grensoverschrijdingen e.d.
- Spähprogramm "Dishfire": NSA analysiert fast 200 Millionen SMS pro Tag Spiegel Online, 16-jan-2014
Adressbücher, Finanztransaktionen, Reisepläne: Solche Informationen zieht die NSA offenbar massenhaft aus Mobiltelefonen ab. Laut Guardian zeigt eine Präsentation aus dem Jahr 2011, dass der US-Geheimdienst täglich millionenfach SMS abgriff
- Britse geheime dienst heeft toegang tot sms-database NSA | nrc.nl, 16 -jan-2014
- NSA collects millions of text messages daily in 'untargeted' global sweep | theguardian.com, 16-jan-2014
NSA extracts location, contacts and financial transactions from up to 200 million texts daily that GCHQ can tap into to search metadata from UK numbers
| NSA Dishfire presentation on text message collection - key extracts | The GuardianContent Extraction Enhancements For Target Analytics: SMS Text Messages: A Goldmine to Exploit, 9 June, 2011
FASCIA - NSA
- NSA tracking cellphone locations worldwide, Snowden documents show | The Washington Post, 4-dec-2013 | FASCIA: The NSA's huge trove of location records
FASCIA is the National Security Agency's enormous database containing trillions of device-location records that are collected from a variety of sources. This document shows the volume and types of device-location data collected by the agency
MAINWAY - NSA
- NSA can eavesdrop traffic in Real Time, more PRISM slides leaked | The Hacker News, 30-jun-2013
Two of the new slides detail the data collection process, from the initial input of an agency analyst, to data analysis under several previously-reported analysis tools such as Marina (internet data), Mainway (call records), Nucleon (voice data), and Pinwale (video data)
- MAINWAY | Wikipedia
MARINA - NSA
- NSA stores metadata of millions of web users for up to a year, secret files show | The Guardian, 30-sep-2013
• Vast amounts of data kept in repository codenamed Marina
• Data retained regardless of whether person is NSA target
• Material used to build 'pattern-of-life' profiles of individuals
• What is metadata? Find out with our interactive guide - MARINA | Buggedplanet.info
MUSCULAR - NSA
- How the NSA's MUSCULAR program collects too much data from Yahoo and Google | The Washington Post, 30-okt-2013
This document is an excerpt from Special Source Operations Weekly, an internal National Security Agency publication dated March 14, 2013. It describes a common NSA problem of collecting too much information and how the agency is attempting to control it
- Excerpt from SSO Weekly on Windstop, Muscular, Incenser | Cryptome, okt-2013 [pdf]
- NSA's MUSCULAR Project and the Importance of Encryption Key Management | CipherCloud.com
What lessons do recent NSA Muscular revelations offer to enterprises considering cloud adoption? Encryption key management puts enterprises in control.
MYSTIC - NSA
- NSA surveillance program reaches 'into the past' to retrieve, replay phone calls | Washington Post, 18-mrt-2014
- NSA kan tot maand terug telefoongesprekken terugluisteren | nrc.nl, 18-mrt-2014
- Description of data collection by NSA under MYSTIC | The Washington Post
This is an excerpt from a weekly briefing memo from the NSA's Special Source Operations team, which is responsible for deploying and maintaining bulk collection methods
- Adding a country to MYSTIC efforts mentioned | The Washington Post
This is an excerpt from the FY13 Congressional Budget Justification for the National Intelligence Program
NSA PROGRAM TO CRACK ONLINE ENCRYPTION
- Belgacom ontdekte al in 2012 problemen | De Standaard, 17-sep-2012
- Shifting Shadow, STORMBREW, Flying Pig: New Snowden documents show NSA deemed Google networks a "target." By Ryan Gallagher | Slate.com, 9-sep-2013
On Sunday, Brazilian TV show Fantastico published previously undisclosed details based on documents obtained by Guardian journalist Glenn Greenwald from former NSA contractor Edward Snowden. The 13-minute news segment focused on the revelation that, according to the leaked files, the NSA apparently targeted Brazil’s state-run Petrobras oil producer for surveillance-undermining a recent statement by the agency that it "does not engage in economic espionage in any domain."
[...]
Aside from targeting Petrobras, Fantastico revealed that in a May 2012 presentation reportedly used by the agency to train new recruits how to infiltrate private computer networks, Google is listed as a target. So are the French Ministry of Foreign Affairs and SWIFT, a financial cooperative that connects thousands of banks and is supposed to help "securely" facilitate banking transactions made between more than 200 countries. Other documents show that the NSA’s so-called STORMBREW program-which involves sifting Internet traffic directly off of cables as it is flowing past-is being operated with the help of a "key corporate partner" at about eight key locations across the United States where there is access to "international cables, routers, and switches." [...]
Now, documents published by Fantastico appear to show that, far from "cracking" SSL encryption-a commonly used protocol that shows up in your browser as HTTPS-the spy agencies have been forced to resort to so-called "man-in-the-middle" attacks to circumvent the encryption by impersonating security certificates in order to intercept data.
Prior to the increased adoption of SSL in recent years, government spies would have been able to covertly siphon emails and other data in unencrypted format straight off of Internet cables with little difficulty. SSL encryption seriously dented that capability and was likely a factor in why the NSA started the PRISM Internet surveillance program, which involves obtaining data from Internet companies directly.
However, in some cases GCHQ and the NSA appear to have taken a more aggressive and controversial route-on at least one occasion bypassing the need to approach Google directly by performing a man-in-the-middle attack to impersonate Google security certificates. One document published by Fantastico, apparently taken from an NSA presentation that also contains some GCHQ slides, describes "how the attack was done" to apparently snoop on SSL traffic. The document illustrates with a diagram how one of the agencies appears to have hacked into a target’s Internet router and covertly redirected targeted Google traffic using a fake security certificate so it could intercept the information in unencrypted format.
Documents from GCHQ’s "network exploitation" unit show that it operates a program called "FLYING PIG" that was started up in response to an increasing use of SSL encryption by email providers like Yahoo, Google, and Hotmail. The FLYING PIG system appears to allow it to identify information related to use of the anonymity browser Tor (it has the option to query "Tor events") and also allows spies to collect information about specific SSL encryption certificates. GCHQ’s network exploitation unit boasts in one document that it is able to collect traffic not only from foreign government networks-but from airlines, energy companies, and financial organizations, too - NSA maakte gebruik van hack IT-bedrijf DigiNotar | NRC.nl, 14-sep-2013
- NSA disguised itself as Google to spy, say reports | CNET News, 12-sep-2013
- Crucial Unanswered Questions about the NSA's BULLRUN Program | EFF, 9-sep-2013
As we work hard to promote encryption on the web through tools like our browser extension HTTPS Everywhere, we also pay close attention to attacks that undermine the security of that encryption. That's why we were dismayed by last Thursday's revelations about the National Security Agency's aggressive efforts to undermine the ability of citizens to communicate securely
- US and UK spy agencies defeat privacy and security on the internet | The Guardian, 6-sep-2013
• NSA and GCHQ unlock encryption used to protect emails, banking and medical records
• $250m-a-year US program works covertly with tech companies to insert weaknesses into products
• Security experts say programs 'undermine the fabric of the internet' - The NSA's Secret Campaign to Crack, Undermine Internet Encryption | ProPublica, 6-sep-2013 Story updated with a response from the Office of the Director of National Intelligence | Why We Published the Decryption Story
- The End of Internet Privacy? Glenn Greenwald On Secret NSA Program to Crack Online Encryption | Democracy Now!, 6-sep-2013
- 'Meer NSA-inbraakprogramma's binnenkort onthuld' | Webwereld, 5-sep-2013
Uit de eerste plenaire bijeenkomst in het Europese onderzoek naar het PRISM- afluisterschandaal blijkt dat er nog meer onthullingen aankomen. Zo heeft de NSA instructieprogramma's voor medewerkers voor het inbreken op thuisnetwerken
- Sigint - how the NSA collaborates with technology companies Document | The Guardian, 5-sep-2013
Document shows how 'signals intelligence', or Sigint, 'actively engages US and foreign IT industries to covertly influence and/or overtly leverage their commercial products' designs'
- N.S.A. Able to Foil Basic Safeguards of Privacy on Web | NYTimes.com, 5-sep-2013
The National Security Agency is winning its long-running secret war on encryption, using supercomputers, technical trickery, court orders and behind-the-scenes persuasion to undermine the major tools protecting the privacy of everyday communications in the Internet age, according to newly disclosed documents
- Project Bullrun - classification guide to the NSA's decryption program Document | The Guardian, 5-sep-2013
Guide for NSA employees and contractors on Bullrun outlines its goals, and reveals that the agency has capabilities against widely-used online protocols such as HTTPS
- The US government has betrayed the internet. We need to take it back Bruce Schneier | The Guardian, 5-sep-2013
The NSA has undermined a fundamental social contract. We engineers built the internet - and now we have to fix it
- Cyber-Angriffe: So gefährdet die NSA die Internet | Spiegel Online, 2-sep-2013
Umstrittene Methoden, aber ein gutes Ziel: Lange galt die NSA in der Technologiebranche als Kämpfer für sichere Infrastruktur. Das war ein Irrglaube. Die neusten Snowden-Enthüllungen zeigen: Die NSA geführdet die Sicherheit, wenn es ihren Zielen dient
PINWALE - NSA
- NSA-Lauschprogramm weiter aktiv | heise online
Das unter der Bush-Regierung gestartete Überwachungssystem läuft laut Geheimdienstexperten auch unter Obama weiter. Einzelheiten gibt es zu einer "Pinwale" getauften Datenbank, in der große Mengen E-Mails durchforstet werden
PRISM - NSA
- PRISM: meer klokkenluiders, bugs, internet vrijheid en statistiek | Sargasso, 22-jun-2013
- Use of Tor and e-mail crypto could increase chances that NSA keeps your data by Dan Goodin | Ars Technica, 21-jun-2013
Using online anonymity services such as Tor or sending encrypted e-mail and instant messages are grounds for US-based communications to be retained by the National Security Agency even when they're collected inadvertently, according to a secret government document published Thursday.
- NSA-Skandal: überwachen die USA Internet-Seekabel? - SPIEGEL ONLINE Wie umfangreich ist das Spähsystem Prism? Microsoft und Facebook sprechen von wenigen Anfragen des Geheimdienstes NSA, der Whistleblower Snowden vom "Vollzugriff". Eine mögliche Erklärung für den Widerspruch: Es gibt den Totalzugriff - aber durch ein anderes, noch umfassenderes Abhörprogramm
- Secret to Prism program: Even bigger data seizure | AP, 15-jun-2013
Interviews with more than a dozen current and former government and technology officials and outside experts show that, while Prism has attracted the recent attention, the program actually is a relatively small part of a much more expansive and intrusive eavesdropping effort
- NSA seizes phone records of Verizon customers | Washington Times. 5-jun-2013
- How is the NSA accessing your data on Google, Facebook and more? | Fox News, 7-jun-2013
Internet companies have long been monitoring the data that covers a person's entire life: e-mail, financial information, health-related searches, family members, and location information. It represents a level of surveillance that was never possible before.
Slides and leaked information provided to The Washington Post reveal that the government has tapped directly into it - Tech Companies Concede to Surveillance Program | NYTimes.com, 7-jun-2013
- Privacy vs national & global intelligence: Dankzij de Washington post is het spionagebeleid van de states weer in het nieuws | 9lives.be, 7-jun-2013
- NSA PRISM: Dissecting the Tech Companies' Adamant Denials of Involvement in Goverment Spying Program | ABC News, 7-jun-2013
- Aktuelle Nachrichten online - FAZ.NET News, Nachrichten und aktuelle Meldungen aus allen Ressorts. Politik, Wirtschaft, Sport, Feuilleton und Finanzen im überblick.
- Datenschutz: Digital ausgeliefert? - Politik - FAZ Jeder Büger sollte sich zunächst selbst fragen, wem er sich digital öfnet. Wer vom Staat erwartet, Freiheit und Sicherheit... jetzt lesen
- TONIGHT: Watch Amy Goodman Discuss NSA Leaks on MSNBC' 'All In With Chris Hayes' | Democracy Now!, 10-jun-2013 | Democracy Now! A daily independent global news hour with Amy Goodman & Juan González
- A Massive Surveillance State: Glenn Greenwald Exposes Covert NSA Program Collecting Calls, Emails | Democracy Now!, 7-jun-2013
The National Security Agency has obtained access to the central servers of nine major Internet companies - including Google, Microsoft, Apple, Yahoo! and Facebook. The Guardian and The Washington Post revealed the top-secret program, codenamed PRISM, after they obtained several slides from a 41-page training presentation for senior intelligence analysts. It explains how PRISM allows them to access emails, documents, audio and video chats, photographs, documents and connection logs. "Hundreds of millions of Americans, and hundreds of millions - in fact, billions of people around the world - essentially rely on the Internet exclusively to communicate with one another," Greenwald says. "Very few people use landline phones for much of anything. So when you talk about things like online chat and social media messages and emails, what you’re really talking about is the full extent of human communication." This comes after Greenwald revealed Wednesday in another story that the NSA has been collecting the phone records of millions of Verizon customers. "They want to make sure that every single time human beings interact with one another ... that they can watch it, and they can store it, and they can access it at any time."
- Projekt Prism: NSA spioniert weltweit Internet-Nutzer aus | Spiegel Online, 7-jun-2013
Die NSA soll Internetnutzer massiv überwachen, abgeschöpft werden angeblich E-Mails, Fotos, Chats, Videos. Große Internetkonzerne sollen die Daten ihrer Nutzer freiwillig an den US-Geheimdienst liefern. Apple, Microsoft und Co. bestreiten die Vorwürfe
- Project Prism: Die Cyberspionage der NSA | Spiegel Online, 7-jun-2013
E-Mails, Fotos, Videos, Chats - der US-Geheimdienst NSA späht offenbar große Teile der digitalen Kommunikation aus. Auch deutsche Nutzer von Anbietern wie Google oder Yahoo könnten betroffen sein. Doch es gibt Mittel, um sich gegen die staatlichen Cyberspione zu wehren
- How Team of Geeks Cracked Spy Trade on Palantir | WSJ.com, 4-sep-2009
From a Silicon Valley office, a group of twenty-something software engineers is building an unlikely following of terrorist hunters at U.S. spy agencies.
One of the latest entrants into the government spy-services marketplace, Palantir Technologies has designed what many intelligence analysts say is the most effective tool to date to investigate terrorist networks. The software's main advance is a user-friendly search tool that can scan multiple data sources at once, something previous search tools couldn't do. That means an analyst who is following a tip about a planned terror attack, for example, can more quickly and easily unearth connections among suspects, money transfers, phone calls and previous attacks around the globe - Prism Overview | Palantir.com
SQUEAKY DOLPHIN - GCHQ
- Snowden docs reveal British spies snooped on YouTube and Facebook Investigations by Richard Esposito, Matthew Cole and Mark Schone, with Glenn Greenwald, Special Contributor | NBC News, 27-jan-2014
The British government can tap into the cables carrying the world's web traffic at will and spy on what people are doing on some of the world's most popular social media sites
TEMPORA - GCHQ
De Engelse geheime dienst GCHQ en de NSA werken samen in het project Tempora. In dit kader werden 200 glasvezelkabels afgetapt, die vanuit Engeland in zee uitkomen, waaronder vermoedelijk ook de uit Duitsland afkomstige TAT-14-kabel. Daarbij wordt de inhoud tot 3 dagen opgeslagen, meta- en verbindingsgegevens tot 30 dagen.
- Information commissioner to meet Home Office about plans to track email and phone use | World news | guardian.co.uk
- NSA leaks: US and Britain team up on mass surveillance: Latest revelations from Edward Snowden show that the state risks crossing ever more ethical and legal boundaries | The Observer, 22-jun-2013
- MI5 feared GCHQ went 'too far' over phone and internet monitoring: Amid leaks from NSA whistleblower Edward Snowden, senior intelligence source reveals worries were voiced in 2008 | The Observer, 22-jun-2013
- Internetüberwachung: Tempora ist schlimmer als Prism | Spiegel Online, 22-jun-2013
Das umstrittene US-Spähprogramm Prism? Ist harmlos im Vergleich dazu, in welchem Umfang ein britischer Geheimdienst unter dem Codenamen Tempora weltweit das Internet ausspioniert - und damit auch deutsche Nutzer. Doch selbst Datenschutzaktivisten halten das Vorgehen für legal
- Britische Internet-Überwachung: Freund liest mit | Spiegel Online, 22-jun-2013
- Überwachungsprogramm Tempora: Es geht um unsere Freiheit Ein Kommentar von Christian Stöcker | Spiegel Online, 23-jun-2013
Das britisch-amerikanische Überwachungsprogramm Tempora markiert einen historischen Wendepunkt. Geheimdienste haben sich, unbemerkt von der Öffentlichkeit, das Potential zur orwellschen Totalüberwachung verschafft. Regierungen haben ihren Wählern gezielt verheimlicht, wie sie beobachtet werden.
In den nächsten Wochen und Monaten wird sich entscheiden, ob die demokratischen Öffentlichkeiten der Welt stark genug sind, sich dem schrankenlosen, totalitären Anspruch westlicher Geheimdienste entgegenzustellen - oder eben nicht.
Die Regierungen der betreffenden Staaten waren dazu offenbar nicht in der Lage. In vollem Bewusstsein, dass sie diese Art von Überwachung demokratisch nicht würden rechtfertigen können, haben sie ihrem Wahlvolk systematisch verheimlicht, was hinter seinem Rücken geschieht. Es ist jetzt an diesem Wahlvolk, sich zu wehren - und an uns, deren Daten als Beifang im Tempora-Netz landen, unsere eigenen Volksvertreter zur Verteidigung unserer Freiheit anzuhalten - Mastering the internet: how GCHQ set out to spy on the world wide web: Project Tempora - the evolution of a secret programme to capture vast amounts of web and phone data | The Guardian, 21-jun-2013
- Prism, Tempora und die Bundesregierung | Spiegel Online, 27-jun-2013
Diplomatische Verwerfungen sind derzeit die auffälligste Folge der Enthüllungen von Edward Snowden. Die USA üben gewaltigen Druck aus, auch wenn Obama den NSA-Whistleblower nicht mit Kampfjets jagen will, wie er ironisch erklärte. Der eigentliche Skandal gerät dabei fast zur Nebensache
- Edward Snowden über Tempora: Macht der britischen Datensauger Von Christian Stöcker | Spiegel Online, 7-jul-2013
- Internetüberwachung Tempora: Geheimdienst zapft Glasfaserkabel an | Spiegel Online, 22-jun-2013
- GCHQ taps fibre-optic cables for secret access to world's communications | The Guardian, 21-jun-2013
Britain's spy agency GCHQ has secretly gained access to the network of cables which carry the world's phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency (NSA).
The sheer scale of the agency's ambition is reflected in the titles of its two principal components: Mastering the Internet and Global Telecoms Exploitation, aimed at scooping up as much online and telephone traffic as possible. This is all being carried out without any form of public acknowledgement or debate.
One key innovation has been GCHQ's ability to tap into and store huge volumes of data drawn from fibre-optic cables for up to 30 days so that it can be sifted and analysed. That operation, codenamed Tempora, has been running for some 18 months.
GCHQ and the NSA are consequently able to access and process vast quantities of communications between entirely innocent people, as well as targeted suspects.
This includes recordings of phone calls, the content of email messages, entries on Facebook and the history of any internet user's access to websites - all of which is deemed legal, even though the warrant system was supposed to limit interception to a specified range of targets - 'Britten tappen kabelverbindingen af, onder codenaam Tempora' | NRC, 21-jun-2013
De Britten tappen hoge hoeveelheden data af en slaan die bovendien tot aan dertig dagen lang op om de materie uit te pluizen en te analyseren. De Britse technische mogelijkheden hebben GCHQ tot een supermacht gemaakt in het vergaren van informatie, zo schrijft de krant. GCHQ zou meer data dan de NSA hebben verzameld. 300 analisten van GCHQ en 250 van de NSA zouden sinds mei vorig jaar op het analyseren van al die data zijn gezet.
De Britten volgen dagelijks zeshonderd miljoen 'telefonische contacten'. Ze tappen tweehonderd glasvezelkabels af en kunnen de informatie uit 46 van deze tegelijkertijd verwerken. Het programma wordt elke dag groter.
Het zijn vooral transatlantische kabels die GCHQ aftapt: kabels die via Brits grondgebied Europa en de VS verbinden. Het aftappen gaat op basis van geheime overeenkomsten met de eigenaren van de kabels. Sommigen van hen krijgen zelfs mogelijk een onkostenvergoeding van GCHQ - U.K. hacked diplomats' phones, emails, Guardian reports - World - CBC News The Guardian newspaper says that the British eavesdropping agency GCHQ hacked into the emails and phones of foreign diplomats at international conferences to get an edge in high-stakes international negotiations
TRACFIN - NSA
- NSA späht internationalen Zahlungsverkehr aus | Spiegel Online, 15-sep-2013
Der Militärgeheimdienst NSA überwacht weite Teile des internationalen Zahlungsverkehrs sowie Banken und Kreditkartentransaktionen. Das geht aus Unterlagen aus dem Archiv von Edward Snowden hervor, die der SPIEGEL einsehen konnte. Danach ist ein NSA-Zweig namens "Follow the Money" für das Ausspähen von Finanzdaten zuständig. Die dort gewonnenen Informationen fließen in eine NSA-eigene Finanzdatenbank namens "Tracfin". 2011 enthielt sie 180 Millionen Datensätze. Beim Gros der Daten, 84 Prozent, handelte es sich um Kreditkartendaten
- NSA überwacht Swift-Banktransfers und Ölkonzern Petrobras | Spiegel Online, 9-sep-2013
TREASUREMAP - NSA
- N.S.A. Report Outlined Goals for More Power by James Risen and Laura Poitras | NYTimes.com, 22-nov-2013
Above all, the strategy paper suggests the N.S.A.'s vast view of its mission: nothing less than to "dramatically increase mastery of the global network."
Other N.S.A. documents offer hints of how the agency is trying to do just that. One program, code-named Treasure Map, provides what a secret N.S.A. PowerPoint presentation describes as "a near real-time, interactive map of the global Internet." According to the undated PowerPoint presentation, disclosed by Mr. Snowden, Treasure Map gives the N.S.A. "a 300,000 foot view of the Internet."
Relying on Internet routing data, commercial and Sigint information, Treasure Map is a sophisticated tool, one that the PowerPoint presentation describes as a "massive Internet mapping, analysis and exploration engine." It collects Wi-Fi network and geolocation data, and between 30 million and 50 million unique Internet provider addresses - code that can reveal the location and owner of a computer, mobile device or router - are represented each day on Treasure Map, according to the document. It boasts that the program can map "any device, anywhere, all the time." - NTOC Treasuremap presentation: "Bad Guys Are Everywhere, Good Guys Are Somewhere!" | Spiegel.de [pdf]
Treasuremap
Massive Internet mapping, exploration, and analysis engine
Capability for building a near real-time, interactive map of the global internet
Map the entire Internet - Any device (limited only by available data), anywhere, all the time
Its Huge
Data Sources
• Open Source Intelligence (OSINT, Open Source / Publicly available Internet Meta-Data) & Academic
• Commercially Acquired
• SIGINT
• Information Assurance
Autonomous System Peering - BGP ... and Registries
29396
UNET Unet Network, the Netherlands
Bring the SIGINT (AS Level)
Red Links: SIGINT Collection access poimts between two ASes
Red Core Nodes: SIGINT Collection access points within AS
Red Ringed Node: Nodes within AS are SIGINT Referenced Treasuremap Search Items
- IP Address
- Routers
- DNS (FQN)
- MAC address / 802.11 BSSID / 802.11 SSID
- IP Prefix / Range (CIDR Notation)
- Registry Netblock
- SIGAD and/or Case Notation
- Country / IP Country Code
- Antonomous System (AS) Number
- Free Text
- Treasuremap Announces a New Release NTOC, Office of Technology Development (V45), 11-jan-2011 | Spiegel.de [pdf]
On 10 January, the Office of Technology Development (V45) released a new version of TREASUREMAP, the global IP network-mapping and -exploration system.
• TREASUREMAP on NSANET
• TREASUREMAP on JWICS
• TREASUREMAP on SIPR
The TREASUREMAP system provides a near real-time, interactive map of the global Internet. "It shows you the public Internet, everywhere, as it is today."
Everyone with access to NSANET or Intelink with a valid PKI certificate can access the system. Type "go TREASUREMAP" in your browser and download the new system today!XKEYSCORE - NSA
Xkeyscore is de krachtige zoekmachine van de NSA. XKeyscore kan in verschillende databestanden naar mails, chats, nummers, ip-adressen en bezochte websites zoeken.
- XKeyscore: Spionagewerkzeug wird von BND und BfV genutzt | Spiegel Online, 21-jul-2013
- XKeyscore presentation from 2008 read in full | World news | theguardian.com Training materials for the NSA's XKeyscore program detail how analysts can use it and other systems to mine enormous agency databases and develop intelligence from the internet
- XKeyscore: NSA tool collects 'nearly everything a user does on the internet' by Glenn Greenwald | The Guardian, 31-jul-2013
• XKeyscore gives 'widest-reaching' collection of online data
• NSA analysts require no prior authorization for searches
• Sweeps up emails, social media activity and browsing history
• NSA's XKeyscore program - read one of the presentations - Building a panopticon: The evolution of the NSA's Xkeyscore: How the NSA went from off-the-shelf to a homegrown "Google for packets." | Ars Technica, 9-aug-2013
- Schneier on Security: XKeyscore 2-aug-2013
- XKeyscore Hinweis von Dr. Ulrich Kampffmeyer, 1-aug-2013 | Competence-site.de
- Presenting XKeyscore: What the NSA Is Still Hiding by Amy Davidson, The New Yorker | ReaderSupportedNews, 1-aug-2013
The N.S.A., it appears, doesn't just turn to its metadata library to see who's been calling a terrorist; it uses it in a coordinated way as one of the magnets to draw people's identities from the Web and gather information about them
- XKEYSCORE presentation, 25-feb-2008 [pdf]
- XKeyscore: NSA tool collects 'nearly everything a user does on the internet' | World news | theguardian.com by Glenn Greenwald | The Guardian, 31-jul-2013
• XKeyscore gives 'widest-reaching' collection of online data
• NSA analysts require no prior authorization for searches
• Sweeps up emails, social media activity and browsing history - XKeyscore presentation from 2008 read in full | World news | theguardian.com Training materials for the NSA's XKeyscore program detail how analysts can use it and other systems to mine enormous agency databases and develop intelligence from the internet
- Überwachung: Das Wichtigste zu Prism und XKeyscore | ZEIT ONLINE | Zeit Online, 22-jul-2013
Wie funktionieren die Spähprogramme Prism, Tempora und XKeyscore? Wer überwacht wen? Wer kontrolliert die Überwacher? Die wichtigsten Fakten im Überblick
- Abhörtechnik: Verfassungsschutz testet NSA-Programm | Zeit Online, 21-jul-2013
Verfassungsschutz und BND dementieren, regelmäßig Daten an die NSA zu übermitteln. Sein Amt teste aber die Software Xkeyscore, sagte Verfassungsschutzpräsident Maaßen
- Datensicherheit: Deutsche Geheimdienste setzen US-Spähprogramm ein | Zeit Online, 20-jul-2013
Onderwerpen
DATA DICTIONARY
Zie Surveillance Data Dictionary - Identity Intelligence: Image Is Everything | NYTimes.com
An excerpt of a document obtained by Edward J. Snowden, a former contractor with the National Security Agency, referring to the agency's use of images in intelligence gathering.
Intelligence data:- Biometric/Biologic - Data that shows an individual's physical or behavioral traits: Face, iris, fingerprints, voice, gait.
- Biographic - Data that documents an individual's life history: Name, DOB, address, school, military.
- Contextual/Behavioral - Data that captures an individual's interactions with the external world: Travel, financial, behaviors, social network
EDWARD SNOWDEN
- Edward Snowden interview - the edited transcript | The Guardian, 18-jul-2014
The whistleblower speaks to Alan Rusbridger and Ewen MacAskill about life in Russia, the NSA culture, his time there and the future of communication.
We constantly hear the phrase "national security" but when the state begins ... broadly intercepting the communications, seizing the communications by themselves, without any warrant, without any suspicion, without any judicial involvement, without any demonstration of probable cause, are they really protecting national security or are they protecting state security?
The critical question is, do we want public policies regulating intelligence agencies, or do we want intelligence agencies that determine their own policies, that determine their own regulations, that we have no control or oversight over? And I think that is a critical distinction - Snowden in robotrollator op TED-podium inclusief complete TED Talk met na 27 minuten Tim Berners-Lee | Webwereld, 19-mrt-2014
- Snowden: Big revelations to come, reporting them is not a crime | Wired UK, 18-mrt-2014
- Edward Snowden: Here's how we take back the Internet Talk Video | TED, mrt-2014
Appearing by telepresence robot, Edward Snowden speaks at TED2014 about surveillance and Internet freedom. The right to data privacy, he suggests, is not a partisan issue, but requires a fundamental rethink of the role of the internet in our lives - and the laws that protect it. "Your rights matter - he say, " because you never know when you're going to need them." Chris Anderson interviews, with special guest Tim Berners-Lee
- 'Klokkenluider Edward Snowden is een immorele einzelgänger' opinie David Brooks, columnist van de NewYork Times | VK, 12-jun-2013
- Edward Snowden, NSA files source: 'If they want to get you, in time they will' by Ewen MacAskill (inclusief video interview) | The Guardian, 10-jun-2013
- Edward Snowden: the whistleblower behind the NSA surveillance revelations by Glenn Greenwald, Ewen MacAskill and Laura Poitras in Hong Kong | The Guardian, 10-jun-2013
The 29-year-old source behind the biggest intelligence leak in the NSA's history explains his motives, his uncertain future and why he never intended on hiding in the shadows
- Edward Snowden comes forward as source of NSA leaks | The Washington Post, 9-jun-2013
Edward Snowden, a 29-year-old Booz Allen Hamilton employee, says he's done nothing wrong in revealing government surveillance programs
INTERNET MONITORING
- NSA Uses Google Cookies to Pinpoint Targets for Hacking | readersupportednews.org, 11-dec-2013
- NSA gebruikt 'cookies' van Google om te spioneren op het internet | Knack.be, 11-dec-2013
- NSA Uses Google Cookies To Pinpoint Targets For Hacking | Slashdot, 11-dec-2013
Hugh Pickens DOT Com writes
"For years, privacy advocates have raised concerns about the use of commercial tracking tools to identify and target consumers with advertisements. The online ad industry has said its practices are innocuous and benefit consumers by serving them ads that are more likely to be of interest to them. Now the Washington Post reports that the NSA secretly piggybacks on the tools that enable Internet advertisers to track consumers, using 'cookies' and location data to pinpoint targets for government hacking and to bolster surveillance"REACTIES
- When Metadata Becomes Megadata: What the Government Can Learn by Aubra Anthony | CDT, 17-jun-2013
- Through the Prism revelation by Kamlesh Bajaj | Indian Express, 17-jun-2013
The world is now discovering that this freedom to connect comes at a very high price, namely, massive surveillance, which instils fear, instead of freedom from fear. In a speech on internet freedom at the Hague in December 2011, Clinton also said that states push plans for surveillance in the name of security. Although it was directed at states like China, Russia, Saudi Arabia and other countries in the Middle East, it now turns out that the US itself is engaged in surveillance on an unprecedented scale, in the name of homeland security
- Time to tame the NSA behemoth trampling our rights by Yochai Benkler | theguardian.com, 13-sep-2013
- Tim Berners-Lee: encryption cracking by spy agencies 'appalling and foolish' | The Guardian, 7-nov-2013
In an interview with the Guardian, he expressed particular outrage that GCHQ and the NSA had weakened online security by cracking much of the online encryption on which hundreds of millions of users rely to guard data privacy.
He said the agencies' decision to break the encryption software was appalling and foolish, as it directly contradicted efforts of the US and UK governments to fight cybercrime and cyberwarfare, which they have identified as a national security priority. Berners-Lee also said it was a betrayal of the technology industry - Retired NSA Technical Director Explains Snowden Docs | Alexaobrien.com, 30-sep-2014
I had an opportunity to attend a presentation by a retired technical director at the NSA, William Binney, which provided context for some of the published documents released by former NSA contractor, Edward Snowden. Because of the public value of Binney's expertise on the subject, I decided to publish his presentation and comments on my website.
Binney also mentions how the current NSA mass surveillance regime differs from aspects of an earlier less expensive program, called THINTHREAD, which both he and the former NSA senior computer scientist, Edward Loomis, invented.
As Tim Shorrock has already reported, the back-end of THINTHREAD was used by the NSA in a later program called STELLARWIND (thereby forgoing front end privacy protections both Binney and Loomis built into their earlier, less expensive system). NSA then "illegally directed" STELLARWIND en masse sans privacy protections on Americans and the rest of the world - KEEP CALM and Carry On: PRISM itself is not a big deal: But yes, Skype's no longer safe ... and keep an eye on GCHQ by Duncan Campbell | The Register, 11-jun-2013
- Noam Chomsky on Snowden & NSA at Wild Wild Left Radio | YouTube, 20-jul-2013
- NSA surveillance is an attack on American citizens, says Noam Chomsky | The Guardian, 19-jun-2013
Governments will use whatever technology is available to combat their primary enemy - their own population, says critic
- Noam Chomsky on the NSA, privacy and more at The American University of Beirut | YouTube, 12-jun-2013
- How the Law is Used to Destroy Equality and Protect the Powerful Author Glenn Greenwald with Noam Chomsky | YouTube, 29-okt-2011, published 5-aug-2013
- Surveillance: Secrets, lies and America's spies | The Economist, 15-jun-2013
- Surveillance: Should the government know less than Google? | The Economist, 11-jun-2013
- Edward Snowden: saving us from the United Stasi of America by Daniel Ellsberg | The Guardian, 10-jun-2013
In my estimation, there has not been in American history a more important leak than Edward Snowden's release of NSA material - and that definitely includes the Pentagon Papers 40 years ago. Snowden's whistleblowing gives us the possibility to roll back a key part of what has amounted to an "executive coup" against the US constitution.
Since 9/11, there has been, at first secretly but increasingly openly, a revocation of the bill of rights for which this country fought over 200 years ago. In particular, the fourth and fifth amendments of the US constitution, which safeguard citizens from unwarranted intrusion by the government into their private lives, have been virtually suspended.
The government claims it has a court warrant under Fisa - but that unconstitutionally sweeping warrant is from a secret court, shielded from effective oversight, almost totally deferential to executive requests. As Russell Tice, a former National Security Agency analyst, put it: "It is a kangaroo court with a rubber stamp." - Congress Is Irrelevant on Mass Surveillance. Here's What Matters Instead by Glenn Greenwald | The Intercept, 19-nov-2014
The boredom of this spectacle was simply due to the fact that this has been seen so many times before-in fact, every time in the post-9/11 era that the U.S. Congress pretends publicly to debate some kind of foreign policy or civil liberties bill. Just enough members stand up to scream "9/11? and "terrorism" over and over until the bill vesting new powers is passed or the bill protecting civil liberties is defeated.
All of that illustrates what is, to me, the most important point from all of this: the last place one should look to impose limits on the powers of the U.S. government is . . . the U.S. government. Governments don't walk around trying to figure out how to limit their own power, and that's particularly true of empires.
But it has been clear from the start that U.S. legislation is not going to impose meaningful limitations on the NSA's powers of mass surveillance, at least not fundamentally. Those limitations are going to come from-are now coming from -very different places:
1) Individuals refusing to use internet services that compromise their privacy.
2) Other countries taking action against U.S. hegemony over the internet.
3) U.S. court proceedings.
4) Greater individual demand for, and use of, encryption - Glenn Greenwald: "Surveillance Breeds Conformity" by Natasha Lennard, Salon | RSN, 3-jan-2014
- What everybody gets wrong about Orwell: The author's ideas about language are much more relevant to the current surveillance scandals than Big Brother by Morten Høi Jensen | Salon, 19-jun-2013
- The Snowden files: why the British public should be worried about GCHQ by John Lanchester | The Guardian, 3-okt-2013
The unkeepable secret
Bear in mind also that these documents were widely circulated: out of the 4.9 million Americans with access to classified information, 480,000 private contractors in the US had the "top-secret" security clearance issued to Snowden.
If hundreds of thousands of people had access to these secrets, how secure were they? The NSA and GCHQ had no idea that Snowden had this material, and apparently still don't know exactly what is in it - which is one reason they've been panicking and freaking out.
But if they didn't know that Snowden had copied it, how could they possibly be sure that someone else hasn't also taken a copy and slipped it to the Chinese or Russians or Iranians or al-Qaida? It was cheeky of Oliver Robbins, deputy national security adviser in the Cabinet Office, to harrumph about "very poor information security practices" on the part of David Miranda, the partner of Guardian journalist Glenn Greenwald who was detained at Heathrow under anti-terror laws.
Our spooks lost at least 58,000 pages of classified documents to a US civilian sitting at a workstation in Hawaii, and did so without realising it had happened. In effect they're saying, "your secrets are safe with us, except when we lose them".
There's one further conclusion to draw from the fact that so many people had access to this material. It means that this story would at some point have come out. A programme of this scale in a modern democracy, involving hundreds of thousands of people with access to the fact of total internet surveillance, was an unkeepable secret. It may be no comfort to Snowden as he faces his future, but someone somewhere would eventually have done what he did. Some dams are fated to burst - Digitale Debatten: Was man von Frank Schirrmacher lernen kann Lobo-Kolumne | Spiegel Online, 18-jun-2014
In einer Demokratie hat man zwei Stimmen: eine auf dem Wahlzettel und eine in der öffentlichen Debatte. Frank Schirrmachers Werk ist eine Anleitung, wie aktive Gesellschaftsgestaltung außerhalb des politischen Apparats funktioniert.
"Okay", sagt die Person in der Fußgängerzone, "diese Totalüberwachung finde ich jetzt auch nicht so super. Aber was kann man schon dagegen tun?" Es ist diese spezielle Mischung aus Hoffnungslosigkeit, Zynismus und Egalhaltung, die zur Verzweiflung führen kann. Bei denen, die für die verfassungsgarantierten Grundrechte eintreten, die genau in diesem Moment durch eine aggressive Spähmaschinerie ignoriert werden.
Das wichtigste Machtinstrument der Öffentlichkeit ist die Debatte. Von Frank Schirrmacher konnte man lernen, wie dieses Instrument funktioniert. Man kann es noch immer. Seine große Leistung war die Inszenierung gesellschaftlich wirksamer Debatten.
Sein Werk ist zugleich eine Anleitung, wie aktive Gesellschaftsgestaltung außerhalb des politischen Apparats funktioniert. Die Aufgabe der nächsten Jahre, womöglich Jahrzehnte, wird sein, das von ihm vorgeführte Debatteninstrumentarium zu nutzen, und zwar für das übergeordnete Ziel, das er verfolgte. Natürlich nicht nur, weil Frank Schirrmacher es verfolgte, sondern weil es für die Entwicklung der Zivilgesellschaft essenziell ist:
die Rückeroberung der demokratischen Macht über die digitale Sphäre - Die Mensch-Maschine: Babyeulen schlagen Snowden Sascha Lobo | Spiegel Online, 25-mrt-2014
Wöchentlich gibt es neue Skandalmeldungen über die Abhör- und Abwehrpraktiken von NSA und GCHQ. Doch selbst das interessierte Publikum ist mittlerweile leicht genervt. Es zeigt sich: Die netzöffentliche Empörung ist politisch nicht nachhaltig
- Privacy under attack: the NSA files revealed new threats to democracy By Eben Moglen | The Guardian, 27-mei-2014
We now know the apparatus of repression has been attached to the democratic state, but our struggle for privacy is far from hopeless.
Our concept of "privacy" combines three things: first is secrecy, or our ability to keep the content of our messages known only to those we intend to receive them. Second is anonymity, or secrecy about who is sending and receiving messages, where the content of the messages may not be secret at all. It is very important that anonymity is an interest we can have both in our publishing and in our reading. Third is autonomy, or our ability to make our own life decisions free from any force that has violated our secrecy or our anonymity. These three - secrecy, anonymity and autonomy - are the principal components of a mixture we call "privacy".
What if every book for the past 500 years had been reporting its readers at headquarters? - Eben Moglen: Snowden and the Future A series of talks by Eben Moglen on the Impact of Edward Snowden's revelations at Columbia Law School in association with Software Freedom Law Center | Part I: Westward the Course of Empire 9-okt-2013 | | Part II: Oh, Freedom 30-okt-2013 | Part III: The Union, May it Be Preserved 13-nov-2013 | Part IV: Freedom's Future 4-dec-2013
- Opting Out From the Corporate State of Surveillance by Ralph Nader | RSN, 26-okt-2013
America was founded on the ideals of personal liberty, freedom and democracy. Unfortunately, mass spying, surveillance and the unending collection of personal data threaten to undermine civil liberties and our privacy rights. What started as a necessary means of reconnaissance and intelligence gathering during World War II has escalated into an out-of-control snoop state where entities both governmental and commercial are desperate for as much data as they can grab. We find ourselves in the midst of an all-out invasion on what's-none-of-their-business and its coming from both government and corporate sources. Snooping and data collection have become big business. Nothing is out of their bounds anymore
- Don't trust your phone, don't trust your laptop- this is the reality that Snowden has shown us John Naughton | The Guardian, 8-mrt-2015
Gemalto has conducted an investigation which concludes that there are "reasonable grounds to believe that an operation by NSA and GCHQ probably happened", but that the attack "only breached... office networks and could not have resulted in a massive theft of sim encryption keys". And even if the intruders had stolen encryption keys, the company claims that "the intelligence services would only be able to spy on communications on second generation 2G mobile networks. 3G and 4G networks are not vulnerable to this type of attack."
Oh yeah? The implication of these latest revelations is stark: the capabilities and ambitions of the intelligence services mean that no electronic communications device can now be regarded as trustworthy. It's not only your mobile phone that might betray you: your hard disk could harbour a snake in the grass, too - 'Online privacy vereist wereldwijde actie, net als bij apartheid' | Security.NL, 28-dec-2013
Het beschermen van de privacy op internet vereist dezelfde wereldwijde actie waardoor er een eind aan de apartheid in Zuid-Afrika kwam, aldus Navi Pillay, mensenrechtencommissaris van de Verenigde Naties. Volgens haar maken veel mensen zich zorgen dat hun privégegevens worden misbruikt
- Why the NSA's attacks on the internet must be made public by Bruce Scheier | The Guardian, 4-okt-2013
Today, the Guardian is reporting on how the NSA targets Tor users, along with details of how it uses centrally placed servers on the internet to attack individual computers. This builds on a Brazilian news story from last week that, in part, shows that the NSA is impersonating Google servers to users; a German story on how the NSA is hacking into smartphones; and a Guardian story from two weeks ago on how the NSA is deliberately weakening common security algorithms, protocols, and products.
The common thread among these stories is that the NSA is subverting the internet and turning it into a massive surveillance tool. The NSA's actions are making us all less safe, because its eavesdropping mission is degrading its ability to protect the US - Our Newfound Fear of Risk Schneier on Security blog, 3-sep-2013
We have spent over one trillion dollars and thousands of lives fighting terrorism in the past decade -- including the wars in Iraq and Afghanistan -- money that could have been better used in all sorts of ways. We now know that the NSA has turned into a massive domestic surveillance organization, and that its data is also used by other government organizations, which then lie about it. Our foreign policy has changed for the worse: we spy on everyone, we trample human rights abroad, our drones kill indiscriminately, and our diplomatic outposts have either closed down or become fortresses. In the months after 9/11, so many people chose to drive instead of fly that the resulting deaths dwarfed the deaths from the terrorist attack itself, because cars are much more dangerous than airplanes
- Before Prosecuting Snowden, Investigate the Government Bruce Schneier | NYTimes.com, 11-jun-2013
Was the program he exposed legal and constitutional? Was its classification legal? And was he exposing government deceit?
I believe that history will hail Snowden as a hero -- his whistle-blowing exposed a surveillance state and a secrecy machine run amok. I'm less optimistic of how the present day will treat him, and hope that the debate right now is less about the man and more about the government he exposed - Another Shakeup In Intelligence-But Will It Really Make Much Difference? by I.F. Stone in IF Stone's Bi-Weekly, 29-nov-1971, p 3
Intelligence operations of the Dept. of Defense have grown beyond actual needs of the Dept. and are now receiving an inordinate share of its fiscal resources . . . The same information is sought and obtained by various means and organizations . . . Far more material is collected than essential.
Material is collected which cannot be evaluated in a reasonable length of time and is therefore wasted - The NSA's metastasised intelligence-industrial complex is ripe for abuse: Where oversight and accountability have failed, Snowden's leaks have opened up a vital public debate on our rights and privacy by Valerie Plame Wilson and Joe Wilson | The Guardian, 23-jun-2013
- After Edward Snowden's revelations, why trust US cloud providers? | The Observer, 15-sep-2013
- With Confirmed NSA Spying: Private Briefings Will Begin, But Public Discussions and Public Investigations Must Prevail | EFF, 13-jun-2013
- Prism Could Be a Watershed Moment for Privacy Legislation: Or, It Could Take the Focus Off Advertising Entirely | Advertising Age, 10-jun-2013
- Gespräch mit Frank Rieger vom CCC: Der Zugriff auf die Informationen ist total | Frankfurter Allgemeine, 7-jun-2013
- PGP-Erfinder Phil Zimmermann über NSA im Interview | Spiegel Online, 27-sep-2013
- Wehrt Euch: Die Wissenschaftlerin Shoshana Zuboff ruft zum Widerstand gegen den digitalen Überwachungsstaat auf! | ARD, 20-okt-2013
Wir waren unendlich naiv. Wir dachten immer, Geheimdienste überwachen nur Terroristen. Google, Facebook und Apple nutzen unsere Daten nur, um uns das Leben leichter zu machen. Tatsächlich können Internetkonzerne und Sicherheitsdienste heute schon vorhersagen, was wir morgen tun werden. Erst jetzt wird uns langsam bewusst, was es bedeutet, dass die wertvollsten Rohstoffe der Welt nicht Gold oder Erdöl sind, sondern unsere Daten. Wir stehen am Anfang einer völlig neuen Epoche des Wirtschaftens. "Wir bewegen uns vom industriellen Zeitalter hin zu einer neuen Art der Wirtschaft, die auf Information basiert", sagt Shoshana Zuboff, Wirtschaftswissenschaftlerin an der Harvard University. "Und die Grundlage dieser Wirtschaftsform ist die Überwachung. Der staatliche Sicherheitsapparat und private Internetfirmen haben ein gemeinsames Interesse, die Kontrolle über unendlich große Datenmengen auszuüben. Das ist extrem beunruhigend."
- Me and my metadata - thoughts on online surveillance | ethan zuckerman.com, 3-jul-2013
ACHTERGROND
- Eavesdropping 101: What can the NSA do? mapping "the NSA surveillance octopus" | ACLU [pdf]
- Recording Everything: Digital Storage as an Enabler of Authoritarian Governments by John Villasenor | Center for Technology Innovation at Brookings, 14-dec-2011 [pdf]
Within the next few years an important threshold will be crossed: For the first time ever, it will become technologically and financially feasible for authoritarian governments to record nearly everything that is said or done within their borders - every phone conversation, electronic message, social media interaction, the movements of nearly every person and vehicle, and video from every street corner. Governments with a history of using all of the tools at their disposal to track and monitor their citizens will undoubtedly make full use of this capability once it becomes available.
[...]
Finally, the use by authoritarian governments of systems that record everything in the complete absence of privacy considerations will lead to a long list of other unforeseen and generally negative consequences. Unfortunately, the residents of those countries, as well as the rest of us, will soon start to find out just what those consequences are - An Illustration of How the NSA Misleads the Public Without Technically Lying | EFF, 29-aug-2013
The Wall Street Journal published an important investigation last week, reporting that the National Security Agency (NSA) has direct access to many key telecommunications switches around the country and "has the capacity to reach roughly 75% of all U.S. Internet traffic in the hunt for foreign intelligence, including a wide array of communications by foreigners and Americans."
- Spies Without Borders Series: Using Domestic Networks to Spy on the World | EFF, 8-jun-2013
Below, we're publishing a series of articles looking into how the information disclosed in the NSA leaks affect the international community and how they highlight one part of an international system of surveillance that dissolves what national privacy protections any of us have, whereever we live
| I. Using Domestic Networks to Spy on the World | EFF, 13-jun-3013 - Under the covers of the NSA's big data effort Tech News and Analysis by Derrick Harris | gigaom.com, 7-jun-2013
There's much debate still to be had over the NSA's recently uncovered data-collection practices, but some of the technologies underlying them are out in the open. Here's what we know already
- Edward Snowden Said Contractors Can "Watch Your Ideas Form as You Type." How Does That Work? | Mother Jones, 11-jun-2013
- Vergeet PRISM Ingebouwde NSA backdoor sinds Windows 95 Anarchiel.com: Vrijheid, maar dan ook echt
- NSAKEY | Wikipedia
- The NSA's Word Games Explained: How the Government Deceived Congress in the Debate over Surveillance Powers | EFF, 11-jun-2013
- Tim Shorrock Asks Why It Took the Washington Post So Long to Investigate the US Intelligence System | Democracy Now!, 19-jul-2010
"With all due respect to the Washington Post - and Dana Priest and Bill Arkin are very good reporters - we have to ask, why did it take them seven years to do this story?" says Tim Shorrock, an investigative journalist and author of Spies for Hire: The Secret World of Intelligence Outsourcing. "Anyone who's been covering intelligence or national security in Washington knows that intelligence has been privatized to an incredible extent." [includes rush transcript]
- The data store: on big data | The Guardian
- Facebook Starts Sharing What It Knows about You | MIT Technology Review
- U.S. Program to Detect Cyber Attacks on Infrastructure by Siobhan Gorman, 8-jul-2010 | WSJ.com
The U.S. government is launching an expansive program dubbed Perfect Citizen to detect cyber assaults on private U.S. companies and government agencies running critical infrastructure such as the electricity grid and nuclear power plants, according to people familiar with the program
- Using Metadata to find Paul Revere Kieran Healy, 9-jun-2013
- The Age of Big Data - Data Mining BBC Horizon documentary | YouTube, 10-apr-2013
- AARC Public Library: Church Committee Reports
These 14 published reports of the Church Committee contain a wealth of information on the formation, operation, and abuses of U.S. intelligence agencies. They were published in 1975 and 1976, after which recommendations for reform were debated in the Congress and in some cases carried out
- Safe Harbor - Organization Information: Apple Inc.
- A prime aim of the growing Surveillance State Glenn Greenwald | Salon.com, 19-aug-2011
As economic anxiety and social unrest increase, control over Internet technology and communication becomes vital
- Endless War and the culture of unrestrained power by Glenn Greenwald | Salon.com, 6-sep-2011
The political and media classes appear to have learned no lesson from America's wild overreaction to the attacks
- The Obama administration's war on privacy - Glenn Greenwald | Salon.com. 27-sep-2010
Two new Obama proposals would dramatically expand the government's already vast surveillance powers.
[...]
In early August, two dictatorial (and U.S.-allied) Gulf states - Saudi Arabia and the United Arab Emirates - announced a ban on the use of Blackberries because, as the BBC put it, "[b]oth nations are unhappy that they are unable to monitor such communications via the handsets." Those two governments demand the power to intercept and monitor every single form of communication. No human interaction may take place beyond their prying ears.
[...]
The tyrannical mentality of the UAE, Saudi and Bush DHS authorities are far from aberrational. They are perfectly representative of how the current U.S. administration thinks as well: every communication and all other human transactions must be subject to government surveillance. Nothing may be beyond the reach of official spying agencies. There must be no such thing as true privacy from government authorities. - UK-NSA-GCHQ SURVEILLANCE: Historical article: The Eavesdroppers by Duncan Campbell and Mark Hosenball in Time Out, 21 May 1976 | Statewatch.org [pdf]
- NSA to Spy on Critical Infrastructure, Says WSJ | Threat Level | Wired.com, 8-jul-2010
The NSA has a new program called Perfect Citizen that lets it monitor the networks of utilities and other critical infrastructure to identify potential electronic attacks, The Wall Street Journal reported Wednesday
- The Rot That Is Washington | RSN.org
'The close ties and cooperation between the internet industry and the US government is one of the key ingredients in how the Surveillance State has been erected.' Glenn Greenwald, Guardian UK
- Correlation Is Main Concern Over Data Verizon Gives NSA | MIT Technology Review
What the NSA can do with Verizon's data on phone calls depends on the other sources it can be combined with
- Stellar Wind (code name) | Wikipedia
- NSA Gets Geeky After Dark, New Docs Show Danger Room | Wired.com
BLACK BUDGET
NSA black budget
- NSA seeks 'groundbreaking' spying powers, new leak reveals CNET News
The US government's spying budget includes funds to invent new technologies 'to defeat adversarial cryptography and exploit Internet traffic,' leaked documents show. Read this article by Seth Rosenblatt on CNET News
- FY 2014 Budget-in-Brief - U.S. Department of Homeland Security [pdf]
- Surveillance vs. Infrastructure: When a Country Falls Apart Cris Sheridan | Financial sense, 21-jun-2013
If you've been watching the news, you may know that billions are being spent each year on developing a hi-tech surveillance network to collect, record, and potentially track or predict you and others across the globe.
How much is being spent exactly? Here are some estimates:
The NSA is one of at least 15 intelligence agencies, and combined the total U.S. intelligence budget in 2012 was $75 billion, said Steve Aftergood, director of the government secrecy program at the Federation of American Scientists, a nonpartisan think tank that analyzes national and international security issues.
Aftergood estimates about 14% of the country's total intelligence budget -- or about $10 billion -- goes to the NSA.
... Gordon Adams, a former White House budget official for national security, said he wouldn't be surprised if NSA's resources are "well north" of $20 billion a year.
Meanwhile, America's infrastructure-as graded by the American Society of Civil Engineers-lies in a serious state of disrepair - The Black Budget: Top secret U.S. intelligence funding: $ 52.6 billion Interactive Graphic | Washington Post
- Black budget summary details U.S. spy network's successes, failures and objectives by Barton Gellman and Greg Miller, 29-aug-2013 | The Washington Post
- Inside the 2013 U.S. intelligence 'black budget' | The Washington Post, aug-2013
The pages in this document appear in the summary of the Office of the Director of National Intelligence's multivolume FY 2013 Congressional Budget Justification - the U.S. intelligence community's top-secret "black budget." It covers many of the high-profile agencies, such as the Central Intelligence Agency and the National Security Agency, as well as lesser-known programs, including those within the Treasury, State and Energy Departments. This budget does not include funding for intelligence-gathering by the military.
Although the government has annually released its overall level of intelligence spending since 2007, it has not divulged how it uses those funds. See detailed breakdowns of how the U.S. government allocates resources across the intelligence community and within individual agencies in the annotated pages below - U.S. spy agencies mounted 231 offensive cyber-operations in 2011, documents show | The Washington Post, 31-aug-2013
- NSA investeert in het breken van HTTPS door Henk-Jan Buist | Webwereld, 30-aug-2013
- NSA neemt routers en switches op de korrel | Webwereld, 5-sep-2013
- Snowden-Dokumente: Geheimes Budget von US-Nachrichtendiensten veröffentlicht 29-aug-2013 | Zeit Online
Die US-Geheimdienste verfügen 2013 über ein geheimes Budget von mehr als 50 Milliarden US-Dollar. Dokumente zeigen nun, welcher Dienst wie viel erhielt - und wofür
Intelligence outsourcing
- Meet the contractors analyzing your private data by Tim Shorrock | Salon, 10-jun-2013
Private companies are getting rich probing your personal information for the government. Call it Digital Blackwater.BR> From Narus, the Israeli-born Boeing subsidiary that makes NSA’s high-speed interception software, to CSC, the "systems integrator" that runs NSA’s internal IT system, defense and intelligence, contractors are making millions of dollars selling technology and services that help the world’s largest surveillance system spy on you. If the 70 percent figure is applied to the NSA’s estimated budget of $8 billion a year (the largest in the intelligence community), NSA contracting could reach as high as $6 billion every year.
But it’s probably much more than that - Digital Blackwater: How the NSA Gives Private Contractors Control of the Surveillance State | Democracy Now!, 11-jun-2013
As the Justice Department prepares to file charges against Booz Allen Hamilton employee Edward Snowden for leaking classified documents about the National Security Agency, the role of private intelligence firms has entered the national spotlight. Despite being on the job as a contract worker inside the NSA's Hawaii office for less than three months, Snowden claimed he had power to spy on almost anyone in the country. "sitting at my desk, certainly had the authorities to wiretap anyone, from you or your accountant to a federal judge, to even the president, if I had a personal email" Snowden told the Guardian newspaper.
Over the past decade, the U.S. intelligence community has relied increasingly on the technical expertise of private firms such as Booz Allen, SAIC, the Boeing subsidiary Narus and Northrop Grumman. About 70 percent of the national intelligence budget is now spent on the private sector. Former NSA director Michael V. Hayden has described these firms as a "Digital Blackwater". We speak to Tim Shorrock, author of the book "Spies For Hire: The Secret World of Outsourced Intelligence." - Spies for hire: A project from CorpWatch, Who's Who in Intelligence Contractors featuring research by Tim Shorrock | Crocodyl - Collaborative research on corporations
- The Spy Who Billed Me | by Tim Shorrock | Mother Jones, jan/feb-2005
In the post-9/11 rush to beef up intelligence, the government has outsourced everything from spy satellites to covert operations -- and well-connected companies are cashing in
BEVEILIGING
- Spionage? Daar hebben we het zelf naar gemaakt Opinie Guido van ' Noordende | Trouw, 24-okt-2013
Alle informatie die onversleuteld in de cloud staat of over het internet wordt verstuurd, kan worden afgeluisterd.
Oplossingen zijn bekend. Informatie moet worden versleuteld.
De overheid kan hierbij normen stellen. Deze 'end-to-end'-beveiliging is er een van. Geen onversleutelde data in de cloud dus, tenzij het echt niet anders kan. Dat heeft bijvoorbeeld gevolgen voor de opslag van medische gegevens. Huisartsen slaan die nu vaak op in centrale databases, maar patiëntgegevens zouden bijvoorbeeld éérst moeten worden versleuteld voordat ze in een datacentrum terechtkomen. Verder is de opslag van documenten van een bedrijf in de cloud geen goed idee. Tenzij ze zijn versleuteld met een sleutel die alleen het bedrijf heeft. End-to-end beveiliging is soms lastiger en duurder, maar het kan wel. Het afluisterschandaal bewijst dat dit moet. - Chiels favoriete privacy-beschermende add-ons
- Virtual Private Networks: wegwezen met digitale overheidsbemoeienis
- Use of Tor and e-mail crypto could increase chances that NSA keeps your data | Ars Technica, 21-jun-2013
- In 6 stappen buiten bereik van PRISM | Computer!Totaal
- In 6 stappen buiten bereik van PRISM | Computerworld
De Amerikaanse NSA en FBI tappen in het PRISM-project verkeer af van buitenlandse internetters. Hoewel het programma ook in Nederland actief blijkt, is de regering Rutte II niet van plan iets te doen. Tijd om zelf tegenmaatregelen te treffen
- DuckDuckGo: Search
- How Dozens of Companies Know You're Reading About Those NSA Leaks | EFF, 17-jun-2013
- ItsHidden ItsHidden.com - A safe, easy, anonymous way to surf the net
- Startpage Web Zoek by Ixquick | StartPage: Geen PRISM. Geen surveillance. Geen achterdeurtjes. Gigantisch aftap schandaal in de V.S. onthuld | StartPage
- Opt out of PRISM, the NSA's global data surveillance program | PRISM-BREAK.ORG
Stop reporting your online activities to the American government with these free alternatives to proprietary software
- How to remain secure against NSA surveillance | Bruce Schneier | theguardian.com, 6-sep-2013
With all this in mind, I have five pieces of advice:
1) Hide in the network. Implement hidden services. Use Tor to anonymize yourself.
2) Encrypt your communications. Use TLS. Use IPsec.
3) Assume that while your computer can be compromised, it would take work and risk on the part of the NSA - so it probably isn't. If you have something really important, use an air gap.
4) Be suspicious of commercial encryption software, especially from large vendors.
5) Try to use public-domain encryption that has to be compatible with other implementations - NSA Prism: Why I'm boycotting US cloud tech - and you should too | The Register
- Itshidden biedt anonieme internettoegang via Nederlandse servers | Tweakers
De site Itshidden.com biedt gratis versleutelde vpn-verbindingen aan. Het systeem is vooral bedoeld om BitTorrent-gebruikers ontraceerbaar te maken, nu de jacht op filesharers wordt geïntensiveerd. De servers van de dienst staan in Nederland
- Jouw data op straat | Tegenlicht
Terwijl Tegenlicht werkt aan een aflevering over welke data bedrijven over jou verzamelen en wat ze daarmee kunnen, lekt Edward Snowden over de NSA. Waar vind je jouw data? Kan je het weghalen?
- Website wijst hoe je van spionage PRISM afkomt | ZDNet.nl
Een digitale burgerrechtenorganisatie lanceert een website die bezorgde burgers alternatieve software en diensten toont die veilig zijn voor de spiedende ogen van PRISM
- Überwachung: Wie Sie im Netz anonym und sicher bleiben | Zeit Online
Die NSA ist schuld: Viele Menschen wollen plötzlich lernen, anonym zu surfen und E-Mails zu verschlüsseln. Ein Update der ZEIT ONLINE-Serie "Mein digitaler Schutzschild"
- NSA-Affäre: "Verschlüsselung ist Bürgerpflicht" von Angela Gruber | Zeit Online, 5-sep-2013
Phil Zimmermann hat die E-Mail-Verschlüsselung PGP erfunden. Im Interview fordert er, gegen den Überwachungsstaat zu kämpfen und Dienste wie WhatsApp zu codieren
Casus
CARNIVORE
Zie bij Sector Inlichtingen- en VeiligheidsdienstenECHELON
Zie bij Sector Inlichtingen- en VeiligheidsdienstenROL VAN DE NSA BIJ DRONE MOORDEN
Zie bij DronesGEMALTO HACK
- Gemalto: geheime diensten probeerden ons te hacken | nrc.nl, 25-feb-2015
- European Lawmakers Demand Answers on Phone Key Theft | The Intercept, 20-feb-2015
- US and UK accused of hacking Sim card firm to steal codes | BBC News, 20-feb-2015
Many of Edward Snowden's allegations have shone a light on complex surveillance tactics by the NSA. But perhaps this latest leak has done more to highlight how a single company is in control of millions of people's private data
- Sim card database hack gave US and UK spies access to billions of cellphones | The Guardian, 19-feb-2015
- GCHQ and NSA Collaborate to Steal the Keys to Your Cellphone | Electronic Frontier Foundation, 19-feb-2015
- The Great SIM Heist: How Spies Stole the Keys to the Encryption Castle | The Intercept, 19-feb-2015
The company targeted by the intelligence agencies, Gemalto, is a multinational firm incorporated in the Netherlands that makes the chips used in mobile phones and next-generation credit cards. Among its clients are AT&T, T-Mobile, Verizon, Sprint and some 450 wireless network providers around the world. The company operates in 85 countries and has more than 40 manufacturing facilities. One of its three global headquarters is in Austin, Texas and it has a large factory in Pennsylvania.
In all, Gemalto produces some 2 billion SIM cards a year. Its motto is "Security to be Free."
With these stolen encryption keys, intelligence agencies can monitor mobile communications without seeking or receiving approval from telecom companies and foreign governments. Possessing the keys also sidesteps the need to get a warrant or a wiretap, while leaving no trace on the wireless provider's network that the communications were intercepted. Bulk key theft additionally enables the intelligence agencies to unlock any previously encrypted communications they had already intercepted, but did not yet have the ability to decrypt.
As part of the covert operations against Gemalto, spies from GCHQ - with support from the NSA - mined the private communications of unwitting engineers and other company employees in multiple countriesLAVABIT
- EFF Has Lavabit's Back in Contempt of Court Appeal | Electronic Frontier Foundation, 24-okt-2013
Federal law enforcement officers compromised the backbone of the Internet and violated the Fourth Amendment when they demanded private encryption keys from the email provider Lavabit, the Electronic Frontier Foundation (EFF) argues in a brief submitted Thursday afternoon to the US Court of Appeals for the Fourth Circuit
- Lavabit's Legal Fight: Should The Feds Have The Right To Break The Internet's Security System? | Forbes, 14-okt-2013
Lavabit's legal fight isn't about Ed Snowden. It's about the Internet's security system, and whether feds should have right to break it
- Lavabit: How One Company Refused to Give FBI "Unrestricted" Access to Emails of 400,000 Customers | Democracy Now!, 7-okt-2013 [incl video]
In August, Lavabit became the first technology firm to shut down rather than disclose information to the U.S. government. Lavabit owner Ladar Levison closed his encrypted email company after refusing to comply with a government effort to tap his customers' information. It is now been confirmed the FBI was targeting National Security Agency leaker Edward Snowden, who used Lavabit's services. But Levison says that instead of just targeting Snowden, the government effectively wanted access to the accounts of 400,000 other Lavabit customers. Levison now says that since first going public, he has been summoned before a grand jury, fined $10,000 for handing over encryption keys on paper instead of digitally, and threatened with arrest for speaking out. The Justice Department began targeting Labavit the day after Snowden revealed himself as the source of the NSA leaks. Levison joins us to discuss his case along with his attorney, Jesse Binnall
- Todesurteil für Verschlüsselung in den USA | heise Security, 4-okt-2013
Die Anordnung eines US-Gerichts, Ermittlungsbeamten den geheimen Schlüssel zu übergeben, mit dem sie Zugriff auf die Daten aller Lavabit-Kunden erhielten, ruiniert den letzten Rest Vertrauen in die amerikanischen Cloud-Anbieter
- 'E-mailprovider Lavabit moest ssl-sleutels overhandigen aan overheid VS' door Joost Schellevis | Tweakers, 3-okt-2013
Niet veel later besloot de Amerikaanse overheid om de ssl-sleutel op te vragen, zodat communicatie tussen de gebruiker en de site ontsleuteld kon worden. Lavabit voerde aan dat de communicatie van alle 400.000 gebruikers dan plotsklaps inzichtelijk zou worden, maar het Amerikaanse Openbaar Ministerie beloofde de rechter dat naar de communicatie van de andere gebruikers niet zou worden gekeken. De rechtbank gaf de aanklagers gelijk, en droeg Lavabit op de sleutels te overhandigen.
Lavabit droeg de sleutel inderdaad over, maar drukte deze met een kleine tekstgrootte af op in totaal elf pagina's. De FBI moest daardoor alle 2560 karakters overtypen om de ssl-sleutel te kunnen gebruiken. Toen de rechter Lavabit opdroeg om de sleutel elektronisch te overhandigen, besloot Lavabit zijn dienstverlening te staken. Oprichter Ladar Levison zei in augustus daartoe te hebben besloten omdat hij niet medeverantwoordelijk wilde zijn voor 'misdaden tegen het Amerikaanse volk'. Dieper mocht hij toen nog niet op de zaak ingaan - Edward Snowden's E-Mail Provider Defied FBI Demands to Turn Over Crypto Keys, Documents Show | Wired.com, 2-okt-2013
- NSA intimidation expanding surveillance state Column by Bruce Schneier | USA Today, 27-aug-2013
If there's any confirmation that the U.S. government has commandeered the Internet for worldwide surveillance, it is what happened with Lavabit earlier this month.
[...]
There it is. If you run a business, and the FBI or NSA want to turn it into a mass surveillance tool, they believe they can do so, solely on their own initiative. They can force you to modify your system. They can do it all in secret and then force your business to keep that secret. Once they do that, you no longer control that part of your business. You can't shut it down. You can't terminate part of your service. In a very real sense, it is not your business anymore. It is an arm of the vast U.S. surveillance apparatus, and if your interest conflicts with theirs then they win. Your business has been commandeered - Email Company Used By Edward Snowden Shuts Down Rather Than Hand Data Over To Feds | Forbes, 8-aug-2013
SWIFT SURVEILLANCE
Zie bij Financiële SectorTOTAL INFORMATION AWARENESS (TIA)
Zie bij Sector Inlichtingen- en VeiligheidsdienstenAFLUISTEREN DOOR AUSTRALIË
- Statement on Indulgence | Prime Minister of Australia 19-nov-2013
House of Representatives, Parliament House, Canberra
Prime Minister
In the past 24 hours there have been calls for Australia to detail our intelligence operations and to apologise for them.
Madam Speaker, the first duty of every government is to protect the country and to advance its national interests.
That's why every government gathers information and why every government knows that every other government gathers information.
Madam Speaker, there is no greater responsibility for a prime minister than ensuring the safety of Australian citizens and the security our borders and that, indeed, is why we do collect intelligence.
National security, Madam Speaker, requires a consistent determination to do what's best for Australia and that's why this government will support the national security decisions of previous ones as we will expect future governments to respect ours.
Madam Speaker, Australia should not be expected to apologise for the steps we take to protect our country now or in the past, any more than other governments should be expected to apologise for the similar steps that they have taken.
Importantly, in Australia's case, we use all our resources, including information, to help our friends and allies, not to harm them.
Similarly, Madam Speaker, Australia shouldn't be expected to detail what we do to protect our country any more than other governments should be expected to detail what they do to protect theirs.
Others should ask of us no more than they are prepared to do themselves.
Madam Speaker, I want to make it absolutely crystal clear that Australia has deep respect for Indonesia, for its government and for its people.
I regard President Yudhoyono as a good friend of Australia, indeed as one of the very best friends that we have anywhere in the world.
That's why, Madam Speaker, I sincerely regret any embarrassment that recent media reports have caused him.
But Madam Speaker, it is in everyone's interests, Indonesia's no less than Australia's‚ that cool heads prevail and that our relationship grows closer, not more distant.
I pledge myself to build the strongest possible relationship with Indonesia.
After all, due to its size, proximity and potential to be an emerging democratic superpower of Asia, it is the most important single relationship that we haveOVERIGE CASUS
- Spyfiles: WikiLeaks entblößt überwachungsindustrie | Spiegel Online, 4-sep-2013
Deutsche und internationale Firmen für Überwachungstechnik werben offenbar auch massiv in autoritären Staaten wie Turkmenistan, Oman oder Kasachstan. Das geht aus Dokumenten hervor, die WikiLeaks jetzt präsentiert hat. Die Enthüller wollen sogar wissen, welche Mitarbeiter wann in welche Länder reisten.
- WikiLeaks: Deutsche Unternehmen werben in Diktaturen für überwachungsprogramme | Zeit Online, 4-sep-2013
- Überwachung: US-Drogenbehörde sammelt mehr Telefondaten als die NSA | Zeit Online, 2-sep-2013
Daten aus bis zu 26 Jahren hält das Mobilfunkunternehmen AT&T für die US-Drogenfahnder vor. Das Geheimprogramm "Hemisphere" ist eine gigantische Vorratsdatenspeicherung
Publikaties
- Top secret NSA by Discovery Channel | YouTube
- Use These Secret NSA Google Search Tips to Become Your Own Spy Agency Threat Level | Wired.com, 8-mei-2013
The National Security Agency produced a book to help its spies uncover intelligence hiding on the web.
| Untangling the Web: A Guide to Internet Research | nsa.gov [pdf]
The 643-page tome, called Untangling the Web: A Guide to Internet Research (.pdf), was just released by the NSA following a FOIA request filed in April by MuckRock, a site that charges fees to process public records for activists and othersOverige Snowden Leaks
- The Intercept
- Surveillance | The Guardian
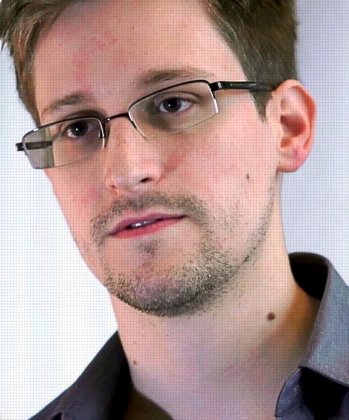 |
Inleiding
Dank zij Edward Snowden weten we dat de inlichtingendiensten op enorme schaal en vaak illegaal het telefoon- en internetverkeer van grote delen van de wereldbevolking afluisteren,dat hiermee miljarden dollars en euro's zijn gemoeid die vooral worden besteed bij particuliere bedrijven,
dat om dit te bereiken de versleuteling van het berichtenverkeer wordt doorbroken, dat bovendien zwakke plekken in die versleuteling worden aangebracht en geëxploiteerd, en dat hierdoor opzettelijk de veiligheid van Internet en van de wereldbevolking in gevaar wordt gebracht.
Op deze webpagina zijn rechtslinks m.b.t. de Snowden Leaks gerangschikt. Voor zover het Nederland en Europa betreft zijn dergelijke links hier te vinden.
Nieuws
Laatst gewijzigd 08 mei 2015
